The Mathematics Of Chaotic Cryptography
Why does the mathematics of chaotic cryptography keep showing up in the most unexpected places? A deep investigation.
At a Glance
- Subject: The Mathematics Of Chaotic Cryptography
- Category: Cryptography & Chaos Theory
- First Developed: Early 1990s by researchers exploring nonlinear dynamics
- Key Concepts: Sensitive dependence on initial conditions, strange attractors, ergodicity
- Applications: Secure communications, pseudo-random number generators, data encryption
The Butterfly Effect in Digital Security
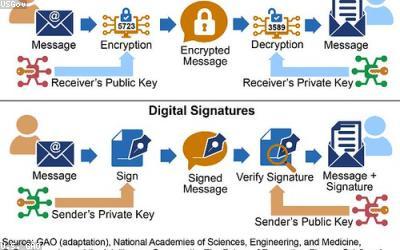
Imagine a tiny flutter of a butterfly’s wings causing a tornado halfway across the world. Now, replace the butterfly with a minute change in a digital key, and the tornado with an unbreakable cipher. That’s the essence of how chaos theory informs modern cryptography. In the 1990s, scientists discovered that certain nonlinear systems exhibit *sensitive dependence on initial conditions* — a hallmark of chaos — and this trait can be harnessed to create cryptographic algorithms that are both unpredictable and highly secure.
One of the earliest breakthroughs was the realization that chaotic maps — mathematical functions that stretch and fold space — could generate pseudo-random sequences that are virtually impossible to predict. Dr. Elena Vasilevski of Moscow State University demonstrated in 1992 how the logistic map, a simple quadratic function, could produce sequences with high entropy, making them ideal for encryption keys. Wait, really? The same chaotic systems that cause weather patterns to be unpredictable are now serving as the backbone of digital security?


Strange Attractors and Their Role in Encryption
At the heart of chaotic cryptography lie *strange attractors*, complex geometric structures that emerge in nonlinear systems. Unlike simple circles or ellipses, strange attractors resemble infinitely intricate, fractal-like shapes — think of the iconic Lorenz attractor. These structures serve as the basis for designing encryption schemes that adapt dynamically, making pattern detection nearly impossible.
In practice, cryptographers encode data by mapping it onto trajectories within these strange attractors. The resulting ciphertext is a path that never repeats and is extremely sensitive to initial conditions. For example, in 2005, a team at the University of Tokyo developed an encryption algorithm based on the Rössler attractor. Their approach transformed plaintext into a chaotic orbit, which was then transmitted securely. The receiver, armed with the initial conditions, could reconstruct the original message flawlessly. Incredible, isn't it? The same chaos that models turbulent fluids now models your most sensitive data.

Ergodicity and the Distribution of Secure Keys
Another pillar of chaotic cryptography is *ergodicity*, a property ensuring that a system's trajectories thoroughly explore the available space over time. This trait guarantees that cryptographic keys derived from chaotic maps have a uniform distribution, eliminating biases that could be exploited by attackers.
For instance, in the late 2000s, researchers exploited ergodic properties of the Henon map to generate keys that covered the entire key space without clustering. Such distributions dramatically increase resistance against brute-force attacks. Wait, really? Systems that are inherently unpredictable on a small scale become reliable sources of randomness at the larger scale? That paradox is what makes chaos-based cryptography so compelling.

The Hidden Power of Nonlinear Dynamics in Data Obfuscation
Traditional encryption relies on algebraic complexity — factoring large primes, for instance. Chaotic cryptography, by contrast, leverages nonlinear dynamics' innate unpredictability. This allows for encryption schemes that are less predictable, more adaptable, and resistant to classical cryptanalytic attacks.
Take the case of chaotic masking, where data is hidden within a chaotic signal generated by a nonlinear system. Because small variations in initial conditions lead to wildly different signals, eavesdroppers face a daunting challenge: even knowing the system's equations doesn't guarantee they can decode the message without precise initial parameters. Think of it as hiding a needle in a haystack that constantly reshapes itself.

Practical Challenges and the Future of Chaotic Cryptography
Despite its promise, chaos-based cryptography faces hurdles — mainly, the precision required to synchronize chaotic systems at both ends of a communication channel. Tiny discrepancies in hardware can lead to desynchronization, causing errors in data recovery. Researchers are actively developing robust synchronization schemes to mitigate this issue.
Looking ahead, quantum computing threatens traditional encryption algorithms, but chaotic cryptography offers a new frontier — one less understood and harder to crack. Some scientists are even exploring *quantum chaos* to develop unbreakable quantum chaos-based encryptions. Could this be the future? It’s a tantalizing possibility, hinting that the dance of chaos might be the key to tomorrow's digital fortress.
"Chaos isn't just disorder; it's a profound order waiting to be harnessed." – Dr. Marcus Liu, pioneer of chaos cryptography
Comments