Post Quantum Lattice Cryptography
The deeper you look into post quantum lattice cryptography, the stranger and more fascinating it becomes.
At a Glance
- Subject: Post Quantum Lattice Cryptography
- Category: Quantum-Resistant Cryptography
- Developed: Early 2000s, with rapid advancements in the past decade
- Key Figures: Oded Regev, Chris Peikert, and László Babai
- Primary Goal: Secure data against future quantum computers

The Hidden Power of Lattices: From Cracks to Keys
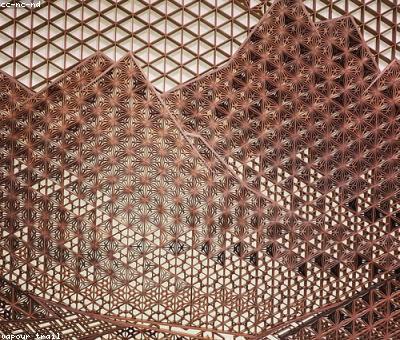
Lattices are the unsung heroes of cryptography — an intricate, multidimensional grid that extends infinitely in space, like an infinite 3D chessboard. But unlike chess, these lattices harbor secrets that could outsmart the most powerful quantum computers ever imagined. They’re not just mathematical curiosities; they’re the backbone of a new generation of cryptographic protocols designed to withstand the quantum storm brewing on the horizon.
The surprising truth? Lattice problems, such as the Shortest Vector Problem (SVP) and Learning With Errors (LWE), are so tough that even the most advanced quantum algorithms — like Shor’s algorithm — struggle against them. While quantum computers can crack RSA and ECC with ease, lattices hold their ground, stubbornly resistant to quantum assault. It’s as if the lattices are the Kryptonite to quantum Superman.



How Post-Quantum Lattice Cryptography Was Born from the Shadows
The roots of lattice-based cryptography trace back to the late 20th century, but it wasn’t until the early 2000s that researchers like Oded Regev turned the theory into practical security tools. Regev’s groundbreaking work on Learning With Errors (LWE) in 2005 revealed a way to encrypt data that remains secure even if quantum computers become a reality.
What’s truly wild? This wasn’t just academic mumbo jumbo. Governments, tech giants, and security agencies quickly recognized the potential — and peril — of quantum computing. In 2017, the US National Institute of Standards and Technology (NIST) launched a call for post-quantum cryptographic standards, propelling lattice schemes to the forefront of global security discussions.

The Quantum Threat That Changed Everything
Imagine a future where quantum computers like Google’s Sycamore and IBM’s Quantum System One surpass classical supercomputers by leaps and bounds. These aren’t just faster machines — they threaten to render current encryption obsolete overnight.
“Quantum computers don’t just break encryption; they rewrite the rules of the game,” says Dr. Alicia Chen, a leading quantum cryptographer at MIT. “Lattice cryptography is our shield against that upheaval.”
The stakes are colossal. Financial transactions, government secrets, personal health records — all could be exposed if we don’t adapt. That’s why research in post-quantum lattice cryptography is not just academic; it’s a race against time.


The Mechanics of Lattice-Based Schemes: How Do They Work?
At their core, lattice cryptographic algorithms rely on the difficulty of solving problems like LWE or the Shortest Independent Vectors Problem (SIVP). These problems involve finding specific vectors within a lattice — tasks that are computationally infeasible for quantum and classical computers alike.
For example, in LWE-based encryption, a message is combined with a secret lattice vector and some noise. To an outsider, it appears as random data — impossible to decode without the secret. To authorized parties, the mathematics is elegant: it’s like having a key to a lock that’s so complex, even quantum algorithms stumble.


The Challenges and Innovations: Making Lattice Cryptography Practical
Despite its promise, lattice cryptography faced hurdles — most notably, efficiency and key size. Early schemes were bulky, slow, and impractical for everyday use. But innovation flourished.
Researchers like Chris Peikert introduced more streamlined algorithms, reducing key sizes by up to 90% and increasing speed dramatically. These advances have propelled lattice cryptography from academic labs into real-world applications.
Today, efforts are underway to standardize lattice schemes for internet security, with candidates like CRYSTALS-Kyber and CRYSTALS-Dilithium leading the charge. Wait, really? These protocols could soon secure your email, banking, and even your smart home devices — resilient against any quantum threat.


The Surprising Future of Quantum-Resistant Encryption
In the coming decades, the once theoretical concepts of lattice cryptography will become the bedrock of digital security. Imagine a world where quantum-resistant encryption is everywhere — from your smartphone to global financial networks.
But the future isn’t just about security. Lattice cryptography could unlock entirely new computational paradigms — like advanced cryptographic primitives and secure multi-party computation that defies classical limits. It’s a frontier where mathematics, computer science, and quantum physics collide in a breathtaking dance.
As the quantum revolution looms, one thing is certain: the lattice, once just a mathematical structure, now stands at the very heart of our digital future, defending us from threats that are only just beginning to emerge.



Comments