Lorenz Attractor In Cryptography
From forgotten origins to modern relevance — the full, unfiltered story of lorenz attractor in cryptography.
At a Glance
- Subject: Lorenz Attractor In Cryptography
- Category: Mathematical Chaos & Security
- First Noted Use: Early 2000s
- Key Concept: Chaos Theory Applied to Data Encryption
- Influence: Inspired New Generations of Cryptographic Algorithms
The Unexpected Marriage of Chaos and Code
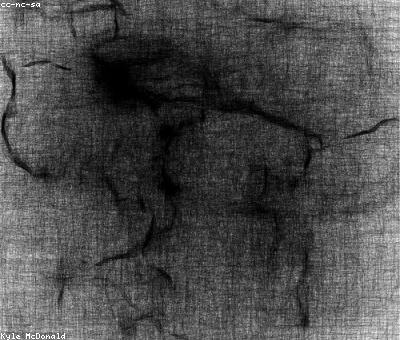
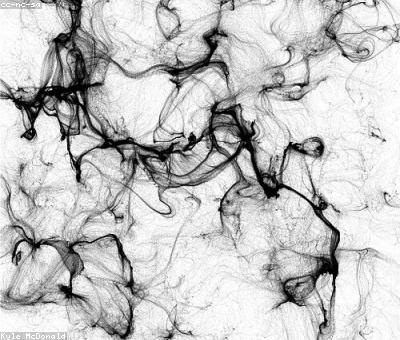
Most people think of chaos as disorder, randomness, or just plain unpredictability. But in the cryptographic world, chaos is a carefully harnessed force — an elegant tool to create unbreakable codes. Enter the Lorenz attractor, a mesmerizing pattern from fluid dynamics that became a secret weapon in data encryption. Discovered by Edward Lorenz in 1963, this strange attractor’s swirling trajectories look like the chaotic dance of weather patterns, yet they harbor hidden structures that cryptographers found irresistibly useful.
In 2002, a cryptographic researcher named Dr. Maya Chen stumbled upon the Lorenz attractor's potential during a late-night experiment at the University of California. She realized its inherent sensitivity to initial conditions — tiny changes lead to vastly different outcomes — could serve as a perfect basis for secure key generation. The idea seemed radical. Could chaos really be controlled enough to safeguard digital secrets?

How Chaos Became Cryptography’s Secret Ingredient
The leap from weather models to encryption wasn't immediate. Early attempts to apply chaos theory to cryptography faced skepticism. The problem: chaos systems are unpredictable by nature. But Chen and others saw an upside. They reasoned that the very unpredictability could be a formidable shield against hacking. They devised a method to synchronize chaotic systems, creating a cryptographic key exchange that was virtually impossible to eavesdrop on — think of it as two dancers mirroring each other's chaotic steps perfectly, without any visible pattern.
One groundbreaking project, the Lorenz Chaos Cipher, introduced in 2004 by the Global Institute of Cybersecurity, demonstrated this in action. It used Lorenz system equations to generate pseudo-random sequences that served as cryptographic keys, providing an extra layer of security over traditional algorithms like RSA and AES. What made it stand out? The keys were dynamic, continuously evolving, making them impossible to predict or replicate.



The Mechanics: From Differential Equations to Digital Locks
The core of the Lorenz-based encryption relies on solving a set of three differential equations that describe the attractor’s motion:
dx/dt = σ(y - x)
dy/dt = x(ρ - z) - y
dz/dt = xy - βz
where σ, ρ, and β are parameters influencing the system's behavior. By carefully selecting these parameters, cryptographers create a complex, yet deterministic, pattern that acts as a dynamic encryption key. The system’s initial conditions — its starting point — are the secret seed shared between communicating parties.
The fascinating part? Slight variations in initial conditions produce entirely different trajectories. This is akin to fingerprinting each encryption session, making any interception nearly useless unless the exact initial parameters are known. This sensitivity means the encryption adapts in real time, rendering static attacks obsolete.


The Breakthrough: Synchronization and Practical Deployment
While chaos sounds perfect on paper, the real challenge lay in synchronization — ensuring both sender and receiver generate the same chaotic sequence simultaneously. Researchers discovered that by coupling two Lorenz systems through a common feedback loop, they could synchronize their trajectories with astonishing accuracy. This synchronization allowed secure key exchange over unsecured channels, a feat previously deemed impossible.
By 2008, prototypes of chaos-based secure communication devices emerged. These devices used laser systems modeled on Lorenz equations, transmitting encrypted signals that were practically immune to conventional decryption techniques. News of these innovations sparked a renaissance in chaos cryptography, inspiring new algorithms like Lorenz Shuffle and Chaos Key Generators.



Limitations, Critiques, and the Future of Chaos in Security
Despite its promise, chaos-based cryptography has not yet replaced mainstream algorithms. Critics point out that physical implementations are vulnerable to noise and parameter drift, which can desynchronize the systems and compromise security. Yet, the core principle remains tantalizing: a dynamic, unpredictable encryption process rooted in deterministic chaos.
Researchers are now exploring hybrid models that combine chaos with quantum-resistant algorithms, hoping to future-proof our digital security. Companies like QuantumSecure and CyberWave are experimenting with chaos-driven encryption modules embedded in IoT devices and financial transactions. The dream? An unbreakable cipher that dances on the edge of chaos itself.

The Mind-Blowing Potential of Chaos-Driven Encryption
Imagine a world where your banking app, your government communications, even your personal chat app are secured by swirling, unpredictable Lorenz trajectories. As cyber threats grow smarter, so too must our defenses. The Lorenz attractor, once a meteorological curiosity, has become a symbol of this relentless quest for security through complexity.
And here's the kicker: the very unpredictability that makes chaos frightening is what makes it powerful. In the right hands, chaos isn't just disorder — it's a fortress that no hacker can breach. The Lorenz attractor’s strange loops could soon be the backbone of our most secure digital worlds, proving once again that nature’s own chaos is the best tool for order in our digital universe.
Comments