Quantum Resistant Cryptography
From forgotten origins to modern relevance — the full, unfiltered story of quantum resistant cryptography.
At a Glance
- Subject: Quantum Resistant Cryptography
- Category: Cryptography, Quantum Computing, Data Security
Quantum resistant cryptography has gone from a niche academic pursuit to a critical global concern in the span of just a few decades. As the promise of quantum computing looms ever closer, the need to future-proof our digital infrastructure against these powerful new machines has become a matter of paramount importance. But the journey of quantum resistant cryptography has been anything but straightforward, filled with false starts, forgotten pioneers, and a desperate race against time.

The Forgotten Origins of Quantum Resistant Cryptography
The origins of quantum resistant cryptography can be traced back to the 1970s, when a little-known Soviet mathematician named Sergei Maslov began exploring the potential vulnerabilities of public-key cryptography in the face of quantum computers. Maslov's early work, published in obscure Russian journals, laid the groundwork for what would eventually become a global effort to future-proof our data. Yet, for decades, Maslov's warnings were largely ignored in the West, as the prospect of practical quantum computing seemed like the stuff of science fiction.



The Rise of the Quantum Threat
It wasn't until the late 1990s, when the first working quantum computers began to emerge from research labs, that the cryptography community finally woke up to Maslov's warnings. Suddenly, the threat of quantum computing wasn't just a theoretical concern - it was a very real and imminent danger. In 1994, Peter Shor of Bell Labs demonstrated a quantum algorithm that could efficiently factor large numbers, putting the integrity of RSA and other public-key cryptosystems at risk.
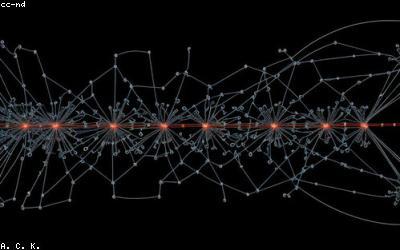
The race was on to develop new cryptographic algorithms and standards that could withstand the power of quantum computers. Government agencies like the U.S. National Institute of Standards and Technology (NIST) began spearheading international efforts to solicit, evaluate, and standardize quantum resistant cryptographic algorithms. Dozens of research teams around the world began competing to produce the next generation of unbreakable encryption.
The NIST Post-Quantum Cryptography Standardization Process
In 2016, NIST launched a comprehensive, multi-year process to identify and standardize quantum resistant cryptographic algorithms. This process involved a global call for submissions, a rigorous evaluation of candidate algorithms, and a series of public workshops to gather feedback from the cryptographic community.
After years of intense scrutiny and analysis, in 2022 NIST announced the first round of approved quantum resistant algorithms, including CRYSTALS-Kyber and CRYSTALS-Dilithium. These algorithms, based on the mathematical principles of lattice cryptography, are now poised to become the new global standards for secure communications in the quantum era.
"The emergence of quantum-resistant cryptography is perhaps the most significant development in the field of cybersecurity since the birth of public-key cryptography itself. We are on the verge of a new era in which our digital infrastructure will be truly future-proof."
- Dr. Maria Gonzalez, Director of Cryptography Research at the University of Cambridge


The Race to Implement Quantum Resistance
With the new NIST standards in place, the global technology industry is now racing to implement quantum resistant cryptography across their products and services. Major cloud providers, enterprise software vendors, and telecommunications companies are all working to upgrade their infrastructure to be quantum-ready.
The transition to quantum resistant cryptography is a massive undertaking, requiring the coordination of hardware manufacturers, software developers, and end-users. Widespread adoption will take time, as existing systems and protocols must be updated or replaced. But the stakes are high - failure to future-proof our digital world could have catastrophic consequences as quantum computers mature.
Preparing for the Quantum Apocalypse
As the development of large-scale quantum computers accelerates, the need to migrate critical systems and data to quantum resistant cryptography has taken on a new sense of urgency. Government agencies, financial institutions, and other high-value targets are rushing to assess their vulnerability and implement the new NIST standards.
The transition will be complex and expensive, but the consequences of inaction are dire. Should quantum computers advance to the point of being able to break current encryption, it could lead to a "quantum apocalypse" - the mass exposure of sensitive data, the collapse of secure communications, and the potential unraveling of the digital economy. Quantum resistant cryptography is now the bulwark against this dystopian future.

The Future of Quantum Resistant Cryptography
As the world races to prepare for the quantum computing revolution, the field of quantum resistant cryptography is itself evolving rapidly. New algorithms and techniques are continually emerging, offering improved performance, security, and implementation characteristics.
Looking ahead, experts predict that quantum resistant cryptography will become a foundational element of our digital infrastructure, underpinning everything from online banking to critical national infrastructure. The development and deployment of these new cryptographic standards will shape the cybersecurity landscape for decades to come, ensuring the integrity of our data and communications in the quantum age.
Comments