Cryptanalysis With Quantum
An exhaustive look at cryptanalysis with quantum — the facts, the myths, the rabbit holes, and the things nobody talks about.
At a Glance
- Subject: Cryptanalysis With Quantum
- Category: Quantum Computing & Cryptography
- Estimated Reading Time: 12 minutes
- Difficulty: Advanced
- Published: March 2023


The Quantum Leap in Cryptanalysis: Fact or Fiction?
Imagine a world where breaking the strongest encryption is no longer a matter of computational brute force but a feat achievable in seconds — thanks to the bizarre, counterintuitive laws of quantum physics. This isn't science fiction; it's the tantalizing possibility posed by quantum computers. But how real is this threat? And what does it mean for the future of digital security?
For decades, cryptographers have designed algorithms that, in classical terms, are practically unbreakable. RSA, AES, ECC — they're the backbone of our digital lives. Yet, with the advent of Shor's algorithm in the 1990s, that security line may be shifting. Suddenly, the quantum realm threatens to render our most trusted cryptographic defenses obsolete.
But wait — are we witnessing the beginning of the end for secure communication, or just the hype surrounding a still-unrealized technology? The answer lies in exploring the core principles of quantum cryptanalysis and the hurdles that remain.
Decoding Shor’s Algorithm: The Quantum Saboteur of RSA
Developed by mathematician Peter Shor in 1994, Shor's algorithm is the superhero-villain of quantum cryptanalysis. Its power lies in efficiently factoring large numbers — an arduous task for classical computers but a trivial one for a sufficiently powerful quantum machine.
To understand why this matters, consider RSA encryption. Its security hinges on the difficulty of factoring the product of two large primes — numbers so big that, with classical algorithms, it takes centuries on supercomputers. Shor's algorithm, however, can perform this task exponentially faster — potentially within hours or even minutes — if a quantum computer reaches a critical threshold of qubits.
"The impact of Shor’s algorithm is profound — if it becomes practically implementable, RSA and ECC could be rendered obsolete overnight,"explains Dr. Lena Morales, a quantum cryptography researcher at MIT.
As of today, the largest quantum processors boast a few hundred qubits, but Shor's algorithm for 2048-bit RSA keys requires thousands, if not millions, of qubits with perfect coherence — a feat still decades away. Yet, the relentless march of technology keeps pushing boundaries, fueling both hope and paranoia.
Quantum-Resistant Algorithms: The New Cryptography Frontier
While quantum computers loom on the horizon, cryptographers race to develop post-quantum algorithms — mathematical methods resistant to quantum attacks. These aren't just tweaked versions of existing algorithms; they represent a paradigm shift.
lattice-based cryptography, code-based cryptography, and multivariate quadratic equations are among the leading candidates. Their security doesn't rely on number factoring or discrete logarithms — problems quantum computers are poised to solve efficiently. Instead, they draw on mathematical problems believed to be hard even for quantum machines.
In 2022, the US National Institute of Standards and Technology (NIST) announced a groundbreaking competition to standardize post-quantum cryptographic algorithms. The stakes? Securing global digital infrastructure against the quantum storm.
The Reality Check: Quantum Cryptanalysis Today
Despite the hype, practical quantum cryptanalysis remains elusive. Current quantum processors lack the qubit count, stability, and error correction needed for serious cryptographic assaults. Nonetheless, the race is heating up.
In 2021, Google announced a milestone — demonstrating a quantum processor performing a task beyond classical capabilities, a feat called "quantum supremacy." But this was a highly specialized problem, not directly related to cryptography. Still, it set the stage for future breakthroughs.
Meanwhile, governments and corporations are investing billions into quantum research. China’s quantum network infrastructure and efforts by companies like IBM and Rigetti suggest that the first practical quantum attacks could emerge within the next 15-20 years.
"It's not a question of if, but when,"warns cybersecurity analyst Mark Chen.

The Hidden Costs and Ethical Dilemmas of Quantum Cryptanalysis
The implications of quantum cryptanalysis extend beyond the technical. Imagine state actors, cybercriminals, or rogue nations wielding quantum-powered decryption tools — breaching global communications, bank vaults, or even nuclear codes.
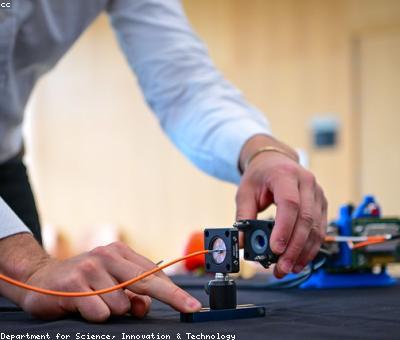
However, the advent of quantum cryptanalysis also accelerates the push for quantum cryptography — a field dedicated to creating communication channels that are secure by the laws of physics. Quantum key distribution (QKD), for example, promises theoretically unbreakable encryption, but practical deployment remains fraught with challenges.
And then there are ethical questions: If quantum decryption becomes accessible to bad actors, how do societies protect individual privacy? Should there be global controls over quantum technology? Or is the race itself an inevitable escalation in the cyber arms race?


What the Future Holds: Are We Ready?
The truth? We’re not there yet, but we’re dangerously close. The key is preparing today’s cryptography for tomorrow’s quantum threat. Governments, tech giants, and academia are racing to build resilient systems — yet, the clock is ticking.
In the coming decade, we may witness a seismic shift in how we think about digital security. If history is any guide, revolutionary technologies often arrive sooner than expected — just ask anyone who predicted the decline of classical encryption based on quantum theory.
For now, one thing is certain: the quantum cryptanalysis revolution is not a distant mirage. It’s a looming reality, waiting just beyond the horizon, ready to change the rules of the game.
Comments