The Future Of Cryptography In The Quantum Age
The untold story of the future of cryptography in the quantum age — tracing the threads that connect it to everything else.
At a Glance
- Subject: The Future Of Cryptography In The Quantum Age
- Category: Quantum Computing, Cryptography, Information Security
In the near future, the rise of quantum computing will revolutionize the world of cryptography as we know it. The same principles that make quantum computers so powerful — their ability to perform calculations across multiple states simultaneously — also threaten to render many of today's encryption standards obsolete. As the world becomes increasingly digitized, the need to safeguard sensitive data has never been more paramount. And in this new era, the future of cryptography will determine the security of our personal information, our financial transactions, and even the foundations of our global communications infrastructure.


The Quantum Threat to Encryption
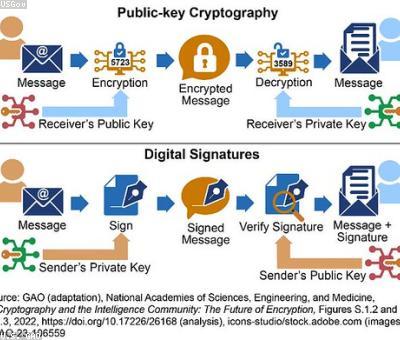
At the heart of the quantum threat to cryptography lies the power of Shor's algorithm, a quantum computing technique developed by mathematician Peter Shor in 1994. Shor's algorithm has the ability to efficiently factor large prime numbers, a feat that is computationally infeasible for classical computers. This is a major problem, as many of the encryption schemes we rely on today, such as RSA and elliptic curve cryptography, are based on the mathematical difficulty of factoring large numbers.
As quantum computers become more powerful, they will be able to easily crack these encryption algorithms, exposing our most sensitive information to potential exploitation. This has sparked a flurry of activity in the cryptography community, as researchers scramble to develop new encryption standards that can withstand the onslaught of quantum computing.
The Quest for Quantum-Proof Cryptography
One of the most promising avenues for quantum-proof cryptography is the field of post-quantum cryptography. These new algorithms are designed to be resistant to attacks by both classical and quantum computers. Some of the leading post-quantum candidates include:
- Lattice-based Cryptography, which relies on the mathematical complexity of finding the shortest vector in a lattice.
- Code-based Cryptography, which uses the difficulty of decoding linear error-correcting codes.
- Multivariate Cryptography, which exploits the complexity of solving systems of multivariate quadratic equations.
These new cryptographic primitives are being rigorously tested and evaluated by the National Institute of Standards and Technology (NIST), which is leading a global effort to standardize post-quantum cryptography and ensure a smooth transition away from our current, vulnerable encryption systems.
"The advent of large-scale quantum computers will break many of the public-key cryptosystems that we rely on today. We must act now to develop new quantum-resistant cryptographic standards." - Dr. Arun Pande, Cryptography Researcher at MIT



The Quantum Internet and the Future of Secure Communication
As quantum computing advances, there is also growing excitement around the potential of quantum cryptography and the "Quantum Internet." Quantum key distribution (QKD) is a technique that allows two parties to produce a shared random secret key known only to them, which can then be used to encrypt and decrypt messages. Unlike classical encryption, QKD is theoretically unbreakable, as any attempt to intercept the key would be detected.
The development of a global "Quantum Internet" based on this technology could revolutionize secure communication, from banking and e-commerce to national security and critical infrastructure protection. Major initiatives are underway around the world to build the foundation for this quantum-secured network of the future.

The Race to Quantum Supremacy
Underlying all of these developments is an intense global competition to achieve "quantum supremacy" — the point at which a quantum computer can perform a specific calculation faster than the world's most powerful classical supercomputers. In 2019, Google claimed to have reached this milestone with its Sycamore processor, which completed a particular calculation in 200 seconds that would have taken the world's fastest classical computer 10,000 years.
As companies and nations race to reach this landmark, the implications for the future of cryptography become increasingly high-stakes. Whichever country or organization is first to achieve practical quantum supremacy will gain a significant advantage in the development of quantum-resistant encryption standards and secure communication networks.
Preparing for the Quantum Future
In the face of these looming threats, governments, businesses, and individuals must take proactive steps to prepare for the quantum age of cryptography. This includes:
- Investing in research and development of post-quantum cryptographic algorithms
- Upgrading critical infrastructure and systems to be quantum-resistant
- Exploring quantum key distribution and other quantum-secured communication technologies
- Educating the public and policymakers about the quantum threat to cybersecurity
The future of our digital world hangs in the balance. But with the right investments and strategic foresight, we can harness the power of quantum computing to build an even more secure and resilient cryptographic infrastructure for the decades to come.
Comments