Steganography Vs Cryptography
Everything you never knew about steganography vs cryptography, from its obscure origins to the surprising ways it shapes the world today.
At a Glance
- Subject: Steganography Vs Cryptography
- Subject: Steganography Vs Cryptography
- Category: Information Security
- First Known Use: 16th Century (Steganography), Ancient Times (Cryptography)
- Key Figures: Johannes Trithemius, Auguste Kerckhoffs
- Related Topics: Data Privacy, Cybersecurity, Digital Watermarking, Steganalysis
At a Glance
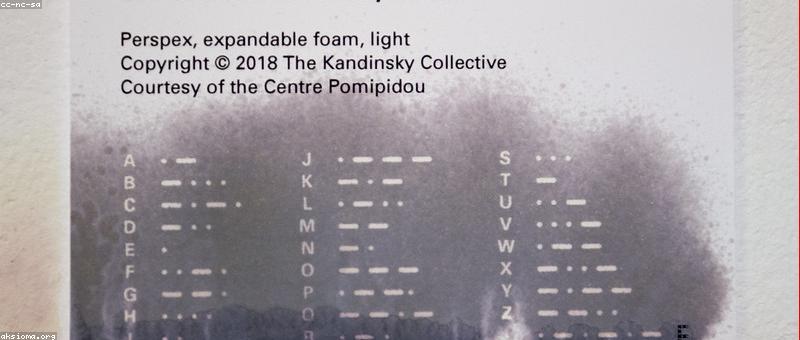
Unmasking the Hidden Art: What is Steganography?
Imagine whispering secrets into the pixels of a digital image or hiding covert messages inside a seemingly innocent audio file. That’s steganography — the ancient art of concealing information in plain sight. Its roots trace back over a thousand years to the Byzantine Empire, where messages were hidden in wax tablets or microdots during wartime. Today, it's the clandestine tool of hackers, whistleblowers, and digital artists alike.
But wait — really? How can something so subtle be effective? The magic lies in the fact that the secret message doesn’t necessarily look different from the original media. A tiny change — like a single pixel’s color value — can embed an entire encrypted document, leaving no visible trace for the untrained eye.
Modern steganography techniques often utilize algorithms to hide data within the least significant bits (LSB) of digital files, ensuring that the visual or auditory quality remains intact. Check out our deep dive into steganography techniques for a fascinating look at how these methods evolved from secret ink to complex digital concealment.
Cryptography: The Science of Secrets
In contrast, cryptography is the art and science of transforming messages into unintelligible gibberish, unless you hold the key. Its origins are shrouded in mystery — some say as early as 1900 BCE with Egyptian hieroglyphs, but it truly blossomed during World War II with the Enigma machine. Cryptography’s purpose is straightforward: protect information from prying eyes, whether in wartime or modern e-commerce.
Cryptographers like Auguste Kerckhoffs, who devised the famous "Kerckhoffs's principles" in 1883, laid the groundwork for modern encryption algorithms. Today, cryptography underpins everything from online banking to secure messaging apps, making it an invisible backbone of digital life.
"Cryptography is the guardian of privacy in the digital age," says cybersecurity expert Lisa Nguyen. "Without it, our personal data would be exposed to hackers and governments alike."
It’s a battle of keys: symmetric encryption uses one key for both encrypting and decrypting, while asymmetric cryptography relies on a public/private key pair. The most renowned example? RSA encryption, which has safeguarded millions of transactions since its invention in 1977 by Ron Rivest, Adi Shamir, and Leonard Adleman.
The War of Wits: When Steganography Meets Cryptography
Here's where things get truly intriguing. While cryptography scrambles a message into an unreadable format, steganography hides that very message inside an innocent file — sometimes even a video or a social media post. Used together, they form an almost invincible security duo.
For example, a covert agent might encrypt a secret document and then hide the encrypted file within an image using steganography. The recipient would extract the image, then decode the message — an intricate two-step dance that leaves no obvious trail.
Did you know that during the Cold War, both superpowers employed this combo? KGB operatives famously embedded encrypted messages inside mundane-looking photographs, which were then smuggled across borders — an espionage technique so effective that it remained secret for decades.
In the digital realm, malware developers increasingly use steganography to evade detection, embedding malicious code inside benign images or audio files. This cat-and-mouse game has led to the rise of steganalysis — the science of detecting hidden information — becoming a critical field in cybersecurity.

The Surprising Evolution of Steganography and Cryptography
While cryptography’s history is well-documented, steganography’s journey from ancient wax tablets to modern digital algorithms is less known. In 2001, researchers at the University of California developed a steganographic algorithm capable of hiding over 1 MB of data inside a standard JPEG image without perceptible loss in quality. This breakthrough made it feasible to transmit sensitive information covertly over social media platforms — think of it as digital invisibility cloaks.
Meanwhile, cryptography saw a renaissance with the advent of quantum computing, threatening to render many encryption methods obsolete. But some experts believe that steganography will become even more critical, providing an additional layer of concealment that quantum-resistant algorithms alone cannot offer.
Interestingly, the line between the two is blurring. Techniques like digital watermarking embed ownership or authenticity data within media files, combining encryption with subtle concealment — an elegant hybrid that’s reshaping security paradigms.

Ethical Dilemmas and the Future of Hidden Data
As steganography and cryptography grow more sophisticated, so do questions about their use. Governments claim they are vital for national security, yet hackers and criminal syndicates exploit them for illicit activities. The debate intensifies around privacy versus security — a battle that shows no signs of ending.
In the future, imagine a world where your selfies secretly contain encrypted health records, or where government agencies use steganography to communicate with undercover agents in hostile territories — without leaving a trace. It’s not just science fiction anymore. Innovations like quantum steganography could revolutionize how we think about privacy and secrecy.
But beware — every new secret technique invites an arms race. As defenders develop new ways to detect hidden messages, malicious actors invent more sophisticated methods to conceal them. The landscape of information concealment is an eternal game of hide and seek.

Who Wins the Hidden Battle?
Ultimately, the contest between steganography and cryptography isn’t about which is better — it’s about how they complement each other. Cryptography ensures your message is unreadable if discovered, while steganography ensures it remains undetectable in the first place.
In a world where data breaches make headlines daily, understanding these secret arts isn’t just for spies and hackers — it’s essential knowledge for anyone serious about privacy. As digital landscapes evolve, so will the strategies of concealment and encryption, forever intertwined in a game of shadows and signals.
Comments