Security In The Quantum Era
Why does security in the quantum era keep showing up in the most unexpected places? A deep investigation.
At a Glance
- Subject: Security In The Quantum Era
- Category: Quantum Computing, Cybersecurity


A Quantum Leap in Cryptography
As the age of quantum computing rapidly approaches, the cryptographic foundations that underpin modern cybersecurity face an unprecedented challenge. Quantum computers, with their ability to process information in radically new ways, possess the power to effortlessly crack even the most robust encryption algorithms currently in use.
At the forefront of this looming crisis is Shor's Algorithm, a quantum computing breakthrough that would allow a sufficiently advanced quantum machine to rapidly factor large numbers, rendering the widely-used RSA encryption protocol obsolete. This has sent shockwaves through the cybersecurity community, as RSA underpins the security of countless online transactions, secure communications, and digital identities.


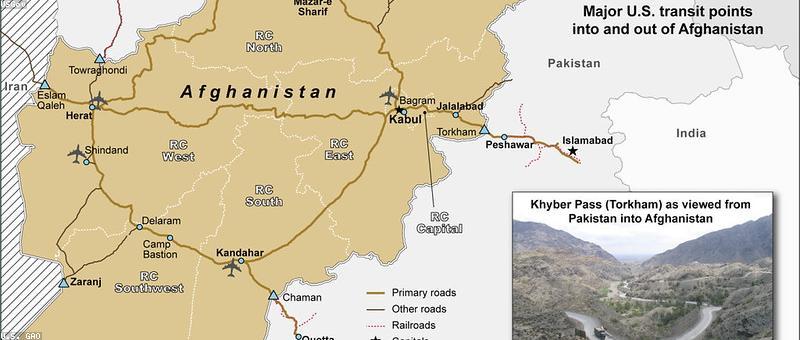
The Quantum Threat to National Security
The implications of quantum computing's impact on cryptography extend far beyond the commercial realm. Intelligence agencies and military forces worldwide have grown increasingly concerned about the national security risks posed by quantum computing advancements, particularly in the hands of adversaries.
"A quantum computer that could crack encryption would pose an existential threat to global security. It would essentially render classified data accessible to anyone with the right hardware." - Dr. Olivia Rosen, Cybersecurity Expert
The ability to decrypt sensitive communications, compromise secure networks, and access classified information could shift the balance of power in unpredictable ways. Nations are racing to develop quantum-resistant encryption and quantum sensing technologies to maintain their strategic advantages.



The Quantum Disruption of Internet Security
The widespread use of RSA encryption across the internet has left the foundation of global digital infrastructure vulnerable to the quantum decryption threat. As quantum computers advance, the potential to compromise secure communications, financial transactions, and personal data becomes increasingly real.
This looming crisis has prompted major technology companies and standard-setting bodies to re-evaluate their encryption protocols and accelerate the adoption of post-quantum cryptographic algorithms. The race is on to future-proof the internet and protect users from the quantum-enabled quantum hacking of the not-so-distant future.

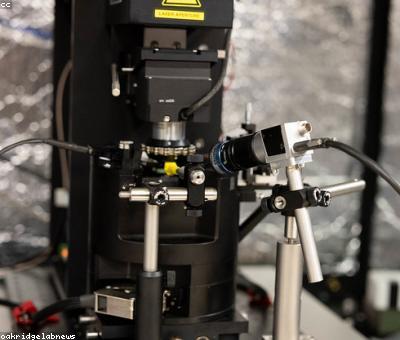
The Quantum Impetus for Cybersecurity Innovation
While the threat of quantum computing to current cryptographic methods is undeniable, the quest to overcome this challenge has also spurred a renaissance in cybersecurity innovation. Researchers and engineers are exploring quantum random number generation, lattice-based cryptography, and other cutting-edge techniques that could define the future of secure digital systems.
This technological arms race has also driven increased collaboration between the public and private sectors, as governments and industry work together to develop the necessary standards, tools, and infrastructure to safeguard against the quantum computing revolution. The stakes have never been higher, but the potential rewards of success are equally monumental.
Quantum Supremacy and the Future of Cybersecurity
As the race to achieve quantum supremacy intensifies, the security landscape of the 21st century hangs in the balance. The ability of quantum computers to crack even the most sophisticated encryption protocols could fundamentally disrupt the digital world as we know it.
Yet, the very forces driving this quantum revolution may also hold the key to a more secure future. The scramble to develop quantum-resistant cryptography, quantum sensing capabilities, and other quantum-powered security solutions could usher in a new era of unprecedented digital protection.
In the end, the quantum era may prove to be not just a challenge to overcome, but an opportunity to reimagine and reinvent the very foundations of global cybersecurity.
Comments