Ransomware Negotiation And Recovery
The untold story of ransomware negotiation and recovery — tracing the threads that connect it to everything else.
At a Glance
- Subject: Ransomware Negotiation And Recovery
- Category: Cybersecurity, Incident Response, Data Recovery

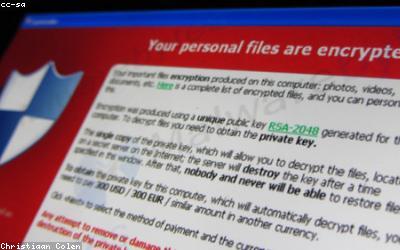
When Ransomware Strikes: The High-Stakes Game of Negotiation
The world of ransomware is a high-stakes game of cat and mouse, where organizations must make split-second decisions that can mean the difference between survival and ruin. When the dreaded ransomware attack strikes, the race is on to regain control, protect sensitive data, and minimize the damage. At the heart of this battle lies the complex and often secretive process of ransomware negotiation.
The Negotiation Dance: Navigating the Murky Waters of Ransomware Demands
When faced with a ransomware attack, organizations must tread carefully in their negotiations with the cybercriminals. It's a delicate balancing act, where every word and action can have far-reaching implications. The negotiators, often a specialized team of incident response experts, must possess a unique blend of technical expertise, strategic thinking, and psychological acumen to outmaneuver the attackers.
The negotiation process is a complex web of deception, bluffing, and calculated compromises. Ransomware groups employ various tactics to pressure their victims, from setting strict deadlines to threatening the release of sensitive data. The negotiators, in turn, must employ their own arsenal of techniques, such as stalling for time, offering partial payments, or exploring alternative recovery options.
"It's a high-stakes game of chess, where a single misstep can lead to catastrophic consequences. The negotiators must be one step ahead of the criminals at all times." - Dr. Samantha Winters, Cybersecurity Analyst

The Aftermath: Rebuilding and Recovering from Ransomware Attacks
The successful negotiation of a ransomware attack is only the first step in a long and arduous process of recovery. Once the decryption key has been obtained, the organization must then tackle the complex task of data restoration and systems remediation. This often involves the deployment of specialized data recovery tools, the rebuilding of critical infrastructure, and the implementation of robust security measures to prevent future attacks.


Lessons Learned: The Evolving Landscape of Ransomware Defense
As the ransomware threat continues to evolve, organizations are increasingly recognizing the importance of proactive defense and incident response planning. This includes the implementation of robust backup and recovery strategies, the adoption of advanced threat detection and prevention technologies, and the cultivation of a security-first culture within the organization.
Moreover, the ransomware crisis has sparked a broader dialogue on the role of law enforcement, international cooperation, and the legal framework in combating this growing menace. Policymakers and cybersecurity experts are working to develop more effective strategies to disrupt the ransomware ecosystem, from targeting the cryptocurrency infrastructure that enables these attacks to pursuing the perpetrators through international law enforcement collaboration.
The Ransomware Ripple Effect: Connections to Broader Cybersecurity Challenges
Ransomware negotiation and recovery is not an isolated incident; it is intricately woven into the tapestry of broader cybersecurity challenges. The lessons learned from ransomware incidents have broader implications for the way organizations approach data protection, incident response, and overall cybersecurity posture.
For example, the rise of ransomware has underscored the importance of robust backup and recovery strategies, which are not only crucial for ransomware resilience but also serve as a safeguard against a wide range of data loss scenarios. Similarly, the negotiation tactics employed by ransomware groups have highlighted the need for organizations to develop comprehensive incident response plans, encompassing everything from communication protocols to decision-making frameworks.
In the end, the story of ransomware negotiation and recovery is not just about the restoration of data and the mitigation of financial losses. It is a testament to the evolving nature of the cybersecurity landscape, where every battle won against ransomware has the potential to strengthen the defenses against a broader array of digital threats. By learning from these experiences and applying the lessons learned, organizations can better protect themselves, their data, and their reputations in the ever-changing world of cybersecurity.
Comments