Ransomware Evolution
Peeling back the layers of ransomware evolution — from the obvious to the deeply obscure.
At a Glance
- Subject: Ransomware Evolution
- Category: Computer Malware, Cybersecurity, Digital Threats


The 2013 Emergence of CryptoLocker
Ransomware first burst into the mainstream in 2013 with the emergence of CryptoLocker, a particularly pernicious piece of malware that encrypted victims' files and demanded a ransom payment to decrypt them. CryptoLocker spread rapidly via phishing emails and exploit kits, quickly making it one of the most widespread and costly cybersecurity threats of the decade.
What made CryptoLocker so devastating was its use of strong encryption algorithms that made the encrypted files nearly impossible to recover without the decryption key held by the attackers. This new "lock and ransom" model proved highly effective, and CryptoLocker was soon followed by a wave of copycat ransomware variants.


The Rise of Ransomware-as-a-Service
As ransomware continued to proliferate, so too did the rise of "Ransomware-as-a-Service" (RaaS) business models. Enterprising cybercriminals began developing and selling ransomware toolkits that even unskilled hackers could use to launch attacks. This democratization of ransomware creation led to an explosion of new variants, with many being tailored to specific industries or regions.
"RaaS made ransomware an accessible weapon for even the most unsophisticated cybercriminals. Suddenly, anyone with a bit of Bitcoin and a grudge could become a ransomware kingpin." - Jane Maloney, Cybersecurity Analyst
The Shift to Targeted Attacks
In the late 2010s, ransomware attacks began shifting away from broad, indiscriminate campaigns in favor of highly targeted strikes against specific organizations. Groups like Ryuk and Sodinokibi carried out reconnaissance to identify high-value targets, then deployed customized ransomware variants tailored to each victim's systems.
This shift to surgical, hand-crafted attacks allowed ransomware operators to extract much larger payouts from victims who could not afford extended downtime or the exposure of sensitive data. It also made the attacks harder to detect and prevent, as they blended in with normal network traffic.
The Rise of Double Extortion
In an effort to increase the leverage over victims, many ransomware groups began adopting a "double extortion" technique in the early 2020s. In addition to encrypting files, they would also steal sensitive data and threaten to publicly release it if the ransom wasn't paid.
This added a new level of psychological pressure, as victims not only faced the prospect of losing access to critical systems, but also the exposure of potentially damaging or embarrassing information. The threat of data leaks pushed many organizations to pay the ransom demands, further incentivizing the use of double extortion tactics.


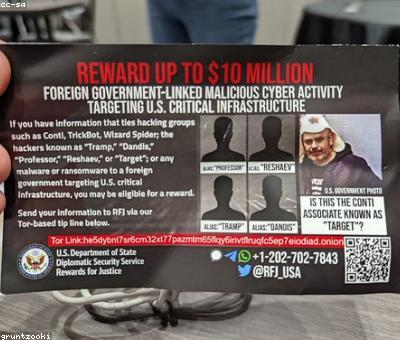
The Emergence of Ransomware Cartels
As ransomware became an increasingly lucrative criminal enterprise, some of the most prolific groups began working together in a coordinated fashion. These "ransomware cartels" pooled their resources, shared intelligence, and even collaborated on joint attacks - blurring the lines between individual ransomware variants.
The rise of these ransomware cartels made the threat even more formidable, as victims faced a unified and relentless opponent. It also complicated attribution and law enforcement efforts, as the various groups could obscure their identities and shift tactics.



The Future of Ransomware
As cybersecurity defenses continue to evolve, ransomware operators are likely to keep innovating and adapting their tactics. Some potential future trends include the use of more sophisticated machine learning and artificial intelligence to automate attacks, the integration of ransomware with other malware like advanced persistent threats, and the targeting of emerging technologies like Internet of Things devices.
One thing is certain: ransomware will remain a persistent and ever-changing threat that organizations of all sizes must remain vigilant against. Staying ahead of the curve will require continuous investment in cybersecurity, threat intelligence, and incident response capabilities.
Comments