Quantum Key Distribution Qkd
The complete guide to quantum key distribution qkd, written for people who want to actually understand it, not just skim the surface.
At a Glance
- Subject: Quantum Key Distribution Qkd
- Category: Quantum Computing, Cryptography


The Quantum Mechanics of Secure Communication
Quantum key distribution (QKD) is a revolutionary cryptographic technique that harnesses the strange laws of quantum mechanics to create an unbreakable encryption system. Unlike traditional public-key cryptography, which relies on mathematical complexity, QKD creates a secret key through the exchange of quantum particles in a way that any eavesdropping is immediately detected.
The basic principle of QKD is surprisingly simple. Two parties, traditionally called "Alice" and "Bob", each have a quantum device that can generate and detect single photons. They use this to establish a shared secret key by sending photons back and forth in a specific quantum state. The laws of quantum mechanics dictate that any attempt to intercept or measure these photons will change their state, alerting Alice and Bob to the presence of an eavesdropper, "Eve".
The Mechanics of a QKD System
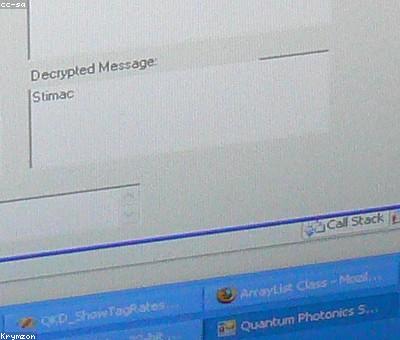
To establish a secret key, Alice and Bob follow a series of steps:
- Quantum Communication: Alice randomly chooses to send each photon in one of two different quantum states, representing the 0 and 1 bits of the key. Bob then randomly measures the state of each photon he receives, recording his results.
- Public Discussion: Alice and Bob then openly communicate over a classical channel (e.g. the internet) to compare notes. They discard any photons where their measurement bases didn't match, leaving them with a partially shared key.
- Error Correction: Since quantum particles are inherently noisy, there may be some disagreement between Alice and Bob's bits. They use error correction techniques to reconcile these differences and arrive at identical keys.
- Privacy Amplification: Finally, Alice and Bob apply a privacy amplification algorithm to distill the final secret key, discarding any remaining information that Eve may have gleaned.


The Rise of Practical QKD
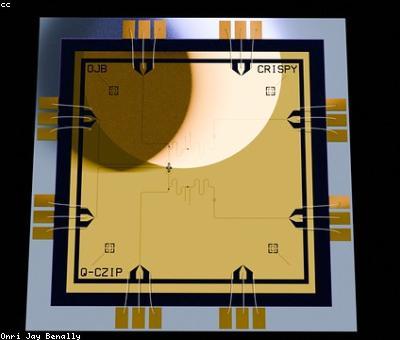
While the concept of QKD has been around since the 1980s, it's only in the past two decades that it has become a practical reality. Advances in single-photon detectors, quantum light sources, and fiber-optic transmission have made QKD systems more reliable, affordable, and scalable.
In 2004, the first commercial QKD network was launched in Geneva, Switzerland, connecting banks, the stock exchange, and government offices. Since then, QKD has been deployed in various settings around the world, from high-security military communications to protecting the privacy of medical data. The Chinese government has been a particularly enthusiastic adopter, building a 2,000-kilometer QKD network across the country.
"Quantum key distribution represents the first commercial application of quantum mechanics. It's the harbinger of a new age of quantum technologies that will transform our world." - Dr. Elise Ricard, Director of the International Quantum Institute
The Limits of QKD
While QKD offers unprecedented security, it does have some practical limitations. The quantum particles used to transmit the key can only travel a certain distance before being corrupted by the environment, limiting the geographic range of a QKD network. There are also challenges around key distribution and the cost of the specialized equipment required.
Furthermore, QKD does not protect against all types of attacks. It is vulnerable to what's known as a "man-in-the-middle" attack, where Eve impersonates both Alice and Bob to intercept the key. Researchers are working on ways to make QKD more resilient to these advanced hacking techniques.

The Future of Quantum Cryptography
As quantum computing advances, the need for quantum-secure communication will only grow. While QKD may have its limitations, it represents a vital stepping stone towards a new era of unbreakable encryption.
Researchers around the world are working to improve the range, speed, and cost-effectiveness of QKD systems. Innovations like "device-independent QKD" and the integration of QKD with 5G networks promise to make this technology more accessible and practical for widespread use.
Beyond QKD, there are other quantum cryptography techniques on the horizon, such as quantum random number generation and quantum digital signatures. The future of secure communication is quantum, and the race is on to bring these innovations out of the lab and into our everyday lives.
Comments