Quantum Cryptography In Practical Use
quantum cryptography in practical use sits at the crossroads of history, science, and human curiosity. Here's what makes it extraordinary.
At a Glance
- Subject: Quantum Cryptography In Practical Use
- Category: Cybersecurity & Quantum Physics
- First Developed: Early 2000s with rapid advancements in the 2010s
- Primary Use: Secure communication channels resistant to hacking
- Key Technologies: Quantum Key Distribution (QKD), Entanglement, Single-photon sources
- Leading Implementations: China’s Micius satellite, European Quantum Networks, U.S. government projects

The Breakthrough That Defied Traditional Limits
Imagine a world where your digital secrets are unbreakable — not by brute force, but by the fundamental laws of nature. That’s the promise of quantum cryptography. It isn’t just an abstract theory anymore; it’s reshaping how governments and corporations defend their most sensitive data.
Since the early 2000s, researchers have been cracking the code of quantum mechanics to develop Quantum Key Distribution (QKD). Unlike classical encryption, which relies on complex algorithms vulnerable to future supercomputers, QKD exploits the no-cloning theorem. This principle says that a quantum state cannot be copied perfectly — making eavesdropping detectable as soon as it occurs.
Real-World Applications That Are Changing the Game
Forget hypothetical scenarios — quantum cryptography is already in action. Banks in Switzerland, government agencies in India, and telecom giants across Europe are deploying QKD links that promise provably secure communications. For example, the European Quantum Internet Alliance is building a network spanning over 3,000 kilometers, linking quantum nodes in major cities.
In Asia, China has established a quantum-secure fiber optic network connecting Beijing, Shanghai, and Guangzhou. This network, operational since 2018, is used for transmitting diplomatic and military communications, effectively making interception impossible.
"Quantum cryptography isn’t just a future concept — it’s a present-day shield for national security,"states Dr. Lin Wei, a leading researcher at Tsinghua University.
Challenges on the Road to Ubiquity
Despite rapid progress, the technology isn’t without hurdles. Distance limitations plague many QKD systems — most work effectively up to 200-300 kilometers over fiber optics before signal degradation occurs. To counter this, scientists are developing quantum repeaters — the quantum equivalent of signal boosters — that could extend reach for thousands of kilometers.
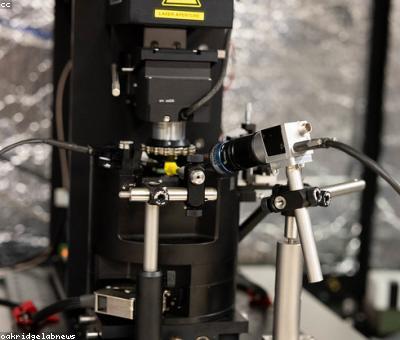
Another challenge is cost. Quantum hardware, such as single-photon detectors and entanglement sources, remains expensive and fragile. Scaling these systems to widespread commercial use demands breakthroughs in manufacturing and maintenance.



Quantum Cryptography vs. Classical Security: The Showdown
Classical encryption — like RSA and AES — has served us well, but it’s ultimately vulnerable. Quantum algorithms, notably Shor’s algorithm, threaten to crack these codes once sufficiently powerful quantum computers arrive. This looming threat has accelerated the push for quantum-resistant algorithms, but none offer the absolute security that quantum cryptography provides today.
In essence, quantum cryptography isn't just an upgrade; it’s a paradigm shift — moving from computational security to **physics-based security** that cannot be bypassed by even the most advanced computers.
Wait, really? Experts believe that within the next decade, quantum networks could be integrated into existing internet infrastructure, creating a hybrid system that leverages both classical and quantum methods for ultimate security.


The Future: From Labs to Everyday Life
Imagine a future where your online banking, personal emails, and confidential business meetings are protected by unbreakable quantum links. That future is rapidly approaching. Companies like ID Quantique and Toshiba are commercializing quantum encryption hardware, with products already available for high-security facilities.
Looking ahead, the integration of quantum internet — a network of interconnected quantum nodes — may revolutionize data sharing, making espionage and data theft relics of the past. Some believe we are on the brink of a quantum revolution comparable to the advent of the internet itself.


Unraveling the Mysteries of Quantum Security
As quantum cryptography becomes mainstream, questions about new attack vectors and vulnerabilities are emerging. While quantum hacking methods like blinding attacks have been demonstrated, they’re limited to specific hardware and can often be thwarted by evolving protocols.
What remains undeniable is that quantum cryptography’s core advantage — detectability of eavesdropping — gives it a strategic edge unmatched by any classical system. The cat-and-mouse game continues, but with a twist: the rules are written by nature itself.
And yet, the most exciting part? We are just scratching the surface of what quantum technologies can achieve. The race to perfect and deploy quantum-secure systems is truly a frontier of human ingenuity and curiosity.


Comments