Quantum Cryptography Explained
Why does quantum cryptography explained keep showing up in the most unexpected places? A deep investigation.
At a Glance
- Subject: Quantum Cryptography Explained
- Category: Cybersecurity & Quantum Physics
- Difficulty: Advanced
- Impact: Revolutionizing secure communication
- First Developed: 1984 by Charles Bennett and Gilles Brassard

The Quantum Leap: How Classical Encryption Meets Its Match
For centuries, encryption was a game of puzzle-solving — complex codes rooted in mathematics that, with enough time and computational power, could be cracked. But in 1984, a groundbreaking breakthrough emerged from the minds of Charles Bennett and Gilles Brassard: quantum cryptography. It promised not just to outwit hackers but to fundamentally change the rules of secure communication forever.
At the core of this revolution is a simple yet mind-bending idea: leveraging the strange, fragile properties of quantum particles — photons, electrons, and atoms — to create unbreakable encryption. Imagine sending a secret message so secure that, if anyone eavesdrops, the very act of listening destroys the message’s integrity. That’s the promise of quantum cryptography, and it is not just science fiction anymore.


Entanglement and the Magic of Quantum Keys
The crux of quantum cryptography lies in a phenomenon called quantum entanglement. When two particles become entangled, their states become intertwined, no matter how far apart they are — distances measured in light-years don't matter. If you measure one particle, the other instantaneously responds, revealing a perfect correlation.
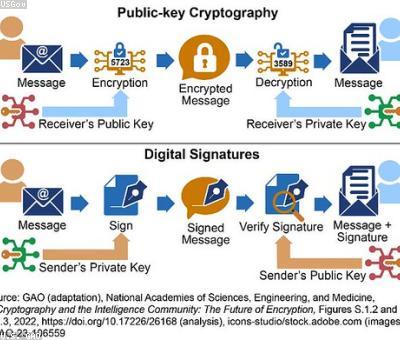
This peculiar property underpins the most famous protocol: Quantum Key Distribution (QKD), specifically the BB84 protocol. Alice and Bob, the classic characters of cryptography tales, generate a shared secret key by transmitting entangled photons. Any eavesdropper, say Eve, trying to intercept the photons, disturbs their quantum state, instantly revealing her presence. The result? A key that’s provably secure — because the laws of physics themselves prevent eavesdropping without detection.
"Quantum mechanics doesn’t just suggest security — it enforces it in the fabric of reality," whispers Dr. Anika Chen, one of today’s leading quantum scientists.
The 1984 Breakthrough That Changed Everything
It’s wild to think that just 40 years ago, quantum cryptography was a theoretical curiosity. Yet, in 1984, Bennett and Brassard published their paper outlining the BB84 protocol — a method so elegant and robust it could ensure perfectly secure communication. This marked the dawn of a new era where the security of data didn't just rely on computational difficulty but on the immutable laws of nature.
Initial experiments started in laboratory settings, with photons bouncing through fiber optic cables over kilometers. By the late 1990s, practical implementations emerged, culminating in the first commercial quantum cryptography systems in 2004. Today, giants like ID Quantique and Toshiba are pushing these systems into real-world applications, from banking to government secrets.


The Challenges of Building a Quantum Fortress
While the promise is tantalizing, building a quantum-secure communication network is riddled with challenges. Photons are notoriously delicate — easily disturbed by temperature fluctuations, vibrations, and even stray electromagnetic fields. Maintaining entanglement over long distances requires complex quantum repeaters, akin to Wi-Fi extenders but exponentially more complicated.
And there’s another hurdle: integration. Existing infrastructure relies on classical networks, and merging them seamlessly with quantum channels remains an ongoing challenge. Nonetheless, nations around the world are racing to establish quantum internet testbeds — an invisible, unhackable web that could someday span the globe.


Quantum Cryptography in the Real World: Current and Future Applications
Today, quantum cryptography isn’t just lab experiments; it’s powering real-world projects. The Swiss city of Geneva has deployed a quantum secure communication network connecting government buildings. China’s Quantum Experiments at Space Scale (QUESS) satellite has successfully demonstrated quantum key exchanges over 1,200 kilometers, shattering previous distance limits.
In the future, quantum cryptography could render traditional encryption obsolete. Imagine banking transactions, military communications, and diplomatic secrets all protected by the immutable laws of physics. The U.S. National Institute of Standards and Technology (NIST) is even developing standards for quantum-safe cryptography, acknowledging the disruptive potential of this technology.


The Ethical and Strategic Implications of Quantum Security
With great power comes great responsibility — and strategic vulnerability. As nations race to dominate quantum encryption, geopolitical tensions escalate. Countries investing heavily in quantum infrastructure may gain unparalleled intelligence capabilities, but the very knowledge of these systems could spur clandestine efforts to develop quantum hacking tools.
Interestingly, some experts argue that the rise of quantum cryptography could also usher in a new era of trust — where espionage becomes nearly impossible, and privacy is redefined in the quantum age. But only time will tell whether the promise of unbreakable security can withstand the political and technological storms ahead.

Why Quantum Cryptography Is Just the Beginning
The true marvel of quantum cryptography isn’t just its current capabilities but the door it opens to a new technological universe. From quantum computing breaking traditional encryption to the potential for quantum-based voting systems and secure cloud computing, the implications are staggering.
And yet, as with all revolutionary technology, it’s a double-edged sword. The same principles that protect us could, in the wrong hands, be used to develop unbreakable cyber weapons. It’s a wild, unpredictable frontier where physics and politics collide — and only the most vigilant will navigate its twists and turns.



Comments