How Ancient Cryptography Shaped Modern Ciphers
The real story of how ancient cryptography shaped modern ciphers is far weirder, older, and more consequential than the version most people know.
At a Glance
- Subject: How Ancient Cryptography Shaped Modern Ciphers
- Category: Cryptography & History
- First Known Use: Around 1900 BCE in Ancient Egypt
- Key Figures: Julius Caesar, Al-Kindi, Auguste Kerckhoffs
- Main Concepts: Substitution ciphers, transposition, key management
- Legacy: Foundations for digital encryption, public key cryptography
At a Glance

The Birth of Cryptography: Secrets Carved in Stone
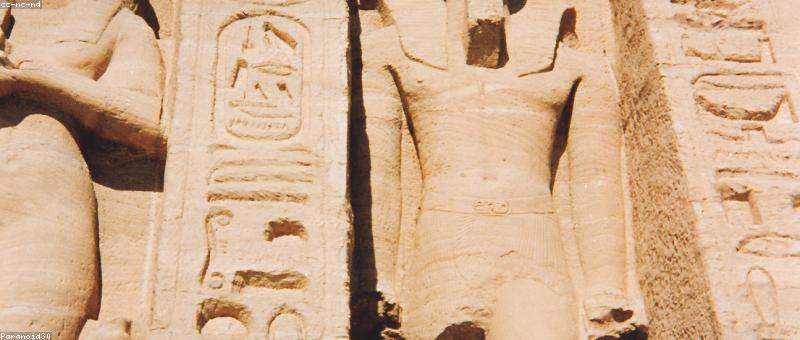
Did you know that the earliest known cryptographic technique dates back over 4,000 years, carved into the walls of an Egyptian tomb? The Khamer workshop, a scribal guild in 1900 BCE, employed simple substitution methods — swapping hieroglyphs to encode messages meant to deter prying eyes. But what’s truly astonishing is how these ancient methods, dismissed as primitive, laid the groundwork for everything we call cryptography today.
Fast forward to 600 BCE, when the Greeks devised the scytale — a wooden rod around which a strip of parchment was wound to create a transposition cipher. The recipient, knowing the diameter of the rod, could simply unwind the parchment to read the message. This device was so effective that it was used by the Spartan military for centuries. The idea that a simple physical device could ensure military secrets? That’s the seed of modern cryptographic hardware.
From Caesar to the Conquerors: The Evolution of Substitution
Jumping to the Roman Empire, Julius Caesar famously used a shift cipher — later known as the Caesar cipher — to encode his dispatches. It was so straightforward that anyone could crack it with a little effort, yet its ingenuity was in its simplicity.
But it wasn’t until the Arab mathematician Al-Kindi in the 9th century that cryptanalysis truly took shape. Al-Kindi wrote the first known treatise on cryptography, explaining how frequency analysis could break simple substitution ciphers. This discovery was revolutionary — it meant ciphers weren’t unbreakable. Cryptography became a game of both creating and defeating codes, an eternal cat-and-mouse chase that still defines the field.
The Birth of Modern Cipher Design: Kerckhoffs’ Principles
In the late 19th century, Auguste Kerckhoffs articulated six principles that would shape modern cipher design. His insistence that the security of a cipher should rely solely on the secrecy of the key, not the algorithm itself, is the cornerstone of contemporary encryption.
Kerckhoffs' work led to the development of the Vigenère cipher, a polyalphabetic cipher that resisted simple frequency analysis. Although later broken, the Vigenère was a significant step forward, demonstrating that complexity and key management could outwit attackers. This balance between complexity and usability remains the essence of modern cryptography.

The Mathematical Turn: From Classical to Computational
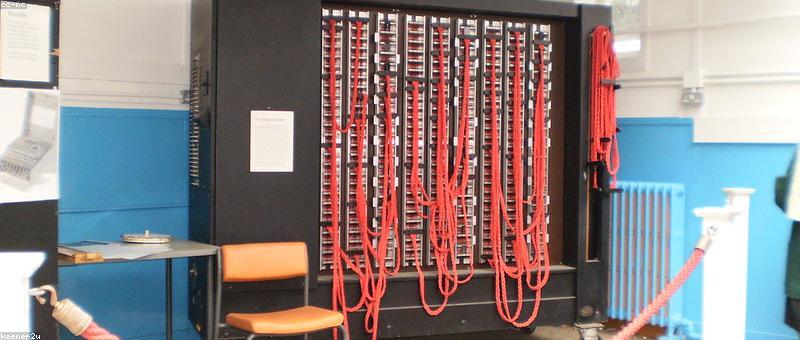
As technology advanced, cryptography moved from physical devices to mathematical algorithms. The 20th century saw the rise of modern cryptography, heavily influenced by the work of Claude Shannon and others. Yet, many concepts trace their roots to ancient ideas — like substitution and transposition — refined through centuries of mathematical evolution.
In the 1970s, the advent of public key cryptography by Whitfield Diffie and Martin Hellman changed everything. Their revolutionary idea that encrypting and decrypting could use different keys was inspired by centuries of cryptanalytic efforts and layered security models. They built upon the ancient principle that complexity could be harnessed — only now, through the power of computational math.


Unexpected Survivors: Ancient Techniques in Modern Use
While modern encryption feels worlds apart from hieroglyph substitutions, surprisingly, some ancient techniques survive in digital form. The simple substitution ciphers echo in the basic algorithms used for hashing and data scrambling. Transposition methods influence the design of complex block ciphers like AES, where data bits are shuffled and substituted to produce chaos — an echo of the ancient scytale.
And here’s the kicker: the core idea that secrecy can be maintained by transforming information — whether by hieroglyphs or binary bits — is unchanged. Ancient cryptography is not just a curiosity; it’s the DNA of all secure communication today.
"Cryptography is history wearing a digital disguise,"— Dr. Lisa Martens, cryptography historian.
The Surprising Legacy of Ancient Code-Making
Consider this: the most secure military and financial systems rely on principles devised thousands of years ago. Every time you see a https:// connection or send a message encrypted with your phone, ancient ideas are humming in the background. The ancient Egyptians, Greeks, and Arabs weren’t just playing with words — they were engineering the building blocks of our digital age.
What’s even more fascinating? Many of the challenges they faced — like keeping secrets safe from spies — are exactly the same today. The only difference is that now, the stakes involve billions of dollars and national security, with algorithms running on quantum computers that ancient scribes could only dream of.


Comments