Historical Cryptanalysis Techniques
Why does historical cryptanalysis techniques keep showing up in the most unexpected places? A deep investigation.
At a Glance
- Subject: Historical Cryptanalysis Techniques
- Category: Cryptography, Military History, Intelligence
- First Developed: Ancient Egypt (circa 1900 BCE)
- Notable Techniques: Frequency Analysis, Known-Plaintext Attacks, Cipher Block Analysis
- Influential Figures: Al-Kindi, William Friedman, Elizabeth Friedman
- Key Locations: Alexandria, Bletchley Park, Washington D.C.
The Roots of Cryptanalysis: From Egyptian Hieroglyphs to Classical Ciphers
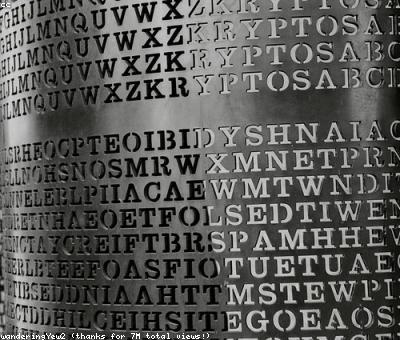
Few realize that the roots of cryptanalysis stretch back over four millennia. The earliest documented efforts emerged in ancient Egypt, where scribes used rudimentary substitution methods for secret communications. But it was in the Islamic Golden Age — around the 9th century — that the first systematic approaches to breaking codes truly took shape. Al-Kindi, often called the father of cryptography, wrote Risalah fi Istikhraj al-Mu’amma (Treatise on the Deciphering of Cryptographic Messages), introducing frequency analysis — an elegant yet devastating technique that would remain effective for centuries.
Imagine the shockwaves of discovering that letter frequency could unravel complex substitution ciphers. For example, the letter 'E' in English appears roughly 12.7% of the time, and Al-Kindi’s insight was that this statistical anomaly could serve as a cryptanalytic "key" to unlock messages that seemed unbreakable. The idea was so revolutionary that it persisted through countless generations of codebreakers, evolving in tandem with the ciphers themselves.
From Caesar to the Renaissance: The Evolution of Cipherbreaking
Fast-forward to the Roman Empire, where Julius Caesar's simple shift cipher was the first major encryption method to be systematically broken. Julius’s *Caesar cipher* was only resistant to casual snooping — yet it spurred cryptanalysts to develop more sophisticated tools. During the Middle Ages, Arab mathematicians refined frequency analysis, while European cryptographers experimented with polyalphabetic ciphers — most notably, the Vigenère cipher.
For centuries, these methods were considered unbreakable — until the 19th century, when the dawn of statistical cryptanalysis began. William and Elizabeth Friedman, a legendary husband-and-wife team, pioneered techniques that would shape modern cryptography. Elizabeth famously cracked the code of the Confederate Confederate cipher during the American Civil War, proving that even complex systems could be vulnerable.
"Cryptanalysis is the art of turning the enemy’s secrets into your advantage — no matter how clever the code." – Elizabeth Friedman
By this time, the techniques had matured from simple letter frequency to include pattern recognition and brute-force attacks. But perhaps the most intriguing development was the advent of the differential cryptanalysis in the 1940s, which exploited how differences in plaintexts could reveal information about the key itself.


The World War II Breakthroughs: From Enigma to Colossus
The 20th century's wars drove cryptanalysis into the spotlight. The Germans’ Enigma machine — used extensively in WWII — seemed unbreakable. But the British, led by Alan Turing and the team at Bletchley Park, cracked it using a combination of mathematical insights and early computing machines. Turing’s work on the Bombe machine, inspired by earlier cryptanalytic principles, was revolutionary — accelerating codebreaking from months to hours.
What’s often overlooked is the use of **crib-based cryptanalysis** — where known or guessed plaintexts (cribs) are used to test hypotheses against ciphertexts. This approach was instrumental in breaking the Lorenz cipher, which was more complex than Enigma. The Germans believed Lorenz was secure, yet British cryptanalysts developed techniques akin to modern differential and linear cryptanalysis to defeat it.
And then came the revelation: the enormous code-breaking effort at Bletchley Park was not just about machines but about **deep understanding of the enemy's logical patterns**. This understanding forms the bedrock of modern cryptanalytic methods still in use today, refined through the advent of electronic computing and machine learning.

Post-War Innovations: The Digital Age and Cryptanalysis Reimagined
The Cold War era brought an explosion of cryptanalytic ingenuity. The development of **linear cryptanalysis** in the 1970s by Mitsuru Matsui was a breakthrough — especially against block ciphers like DES. This technique relies on discovering linear approximations of the cipher's operation, revealing key bits with surprising efficiency.
Yet, one of the most astonishing stories is the revelation of **side-channel attacks** — not about cracking the cipher mathematically but exploiting physical leaks like timing information or electromagnetic emissions. In 1997, researchers demonstrated that by measuring electromagnetic signals from a computer running encryption algorithms, they could recover secret keys. The assumption that cryptography was purely mathematical was shattered — it's now a battlefield of physical and computational security.
Today, quantum cryptanalysis is on the horizon, promising to threaten classical encryption techniques with quantum algorithms like Shor’s algorithm, capable of factoring large integers exponentially faster. This upcoming revolution underscores that cryptanalysis is a constantly evolving cat-and-mouse game, with the past revealing vital clues about the future.


The Little-Known Stories That Changed Everything
Many forget that the earliest cryptanalysts often worked in secrecy, their successes buried in archives or dismissed as luck. But history remembers the turning points — like the 1929 interception of Soviet communications by British spies, which relied heavily on frequency analysis adapted for Russian Cyrillic. Or the 1965 uncovering of the Vietnam War-era Viet Cong codes, which used basic substitution but were vulnerable to early pattern recognition algorithms.
And wait, really? Did you know that during the Cold War, American intelligence agencies secretly employed linguists trained in **cryptanalytic folklore analysis** — studying cultural references, idioms, and dialects — to crack spy communications? That tiny detail often gets overlooked but was crucial in some of the most dramatic espionage successes.

Cryptanalysis Today: An Ongoing Legacy of Ingenuity
From the ancient sands of Egypt to the quantum era, cryptanalysis remains a vibrant, ever-changing battlefield. Today, it’s no longer just about cracking ciphers but also about defending data from malicious actors wielding AI-driven algorithms and hardware exploits. Still, the techniques pioneered by early cryptanalysts — pattern recognition, statistical analysis, physical side-channel attacks — form the backbone of contemporary cybersecurity.
And what’s next? Some speculate that the next breakthrough will come from **biometric cryptography**, where physical traits are used as keys — posing fresh challenges for cryptanalysts eager to decode not just messages but identities. The continuous interplay of innovation and discovery ensures that the history of cryptanalysis will never truly be over; it’s an endless chase that keeps revealing surprises, no matter how well we think we've understood it.
Comments