Frequency Analysis In Ciphers
Most people know almost nothing about frequency analysis in ciphers. That's about to change.
At a Glance
- Subject: Frequency Analysis In Ciphers
- Category: Cryptography & Cryptanalysis
- Difficulty: Advanced
- Key Concepts: Letter frequencies, pattern recognition, cipher-breaking techniques
- Impact: Fundamental tool for decrypting substitution ciphers
The Surprising Power of Letter Frequencies
Imagine trying to crack a code with no clues — no keys, no hints, just a jumble of symbols. Now, imagine if I told you that hidden within this chaos are predictable patterns, universal to all languages, that can act as your secret weapon. This is the essence of frequency analysis, a method so potent it has unraveled some of history's most inscrutable ciphers.
Developed in the 9th century but perfected during the Renaissance, frequency analysis exploits a simple truth: in any given language, certain letters appear far more often than others. For English, the letter e dominates, constituting approximately 13% of all letters used. Meanwhile, letters like q, x, and z are rare rarities. This distribution isn’t random — it's baked into the fabric of the language itself.
What’s truly astonishing? This seemingly mundane fact allows a skilled cryptanalyst to reverse-engineer substitution ciphers with remarkable accuracy. The process, which sounds like detective work, turns out to be a high-stakes game of pattern recognition and educated guesses.


Cracking the Substitution Cipher: The Classic Breakthrough
In 1553, the famous Italian cryptologist Girolamo Cardano published an early treatise revealing how letter frequency could expose encrypted messages. Fast forward to the 19th century, and the technique became a staple in military intelligence, notably during the American Civil War.
Let’s say you’re presented with an encrypted message: "XWZ WZX WZX WZX." The ciphertext appears as a jumble, but a cryptanalyst might note that the same sequence repeats, hinting at a common word or letter pattern. By examining the frequency of symbols, they notice one symbol accounts for about 15% of the total, matching the typical frequency of the letter e.
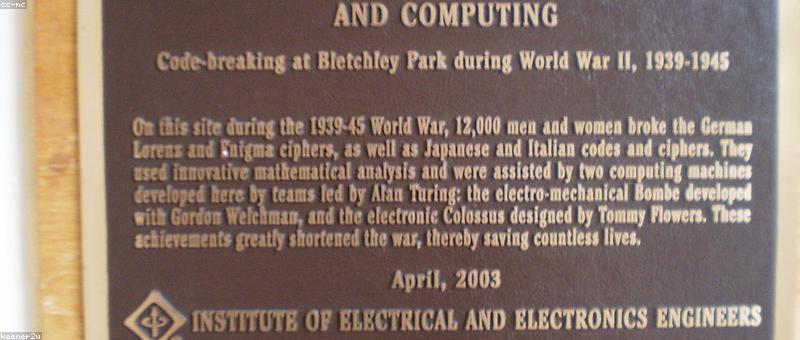
Mapping this symbol to e sets off a cascade of deductions. The next most common symbol might represent t, then a, and so on. Soon, familiar word patterns emerge — like "THE" or "AND" — unlocking the entire message. This methodology was so effective that during WWII, the Allies relied heavily on frequency analysis to decode Nazi ciphers before the advent of computer-based cryptanalysis.

The Limitations and Challenges of Frequency Analysis
While elegant, frequency analysis isn’t foolproof. Modern ciphers, especially one-time pads and complex polyalphabetic systems like the Vigenère cipher, intentionally obscure letter frequencies to thwart analysis.
However, in the 20th century, cryptographers discovered a twist: the repetition of patterns across long ciphertexts reveals clues. The Kasiski examination, devised in 1863, uses repeated sequences to determine key lengths in polyalphabetic ciphers, enabling frequency analysis to be applied even to more advanced encryption.
But beware: modern encryption algorithms, like AES and RSA, employ complex mathematical problems that make frequency analysis useless. Yet, understanding its principles remains crucial for appreciating the evolution of cryptography and the persistent cat-and-mouse game between code-makers and code-breakers.


Real-World Applications and Modern Techniques
Today, frequency analysis isn’t just about deciphering secret messages — it's a foundational concept in data analysis, cybersecurity, and even linguistics. For instance, digital forensic experts often examine character frequency in malware code to identify malicious scripts, since many malware authors reuse code snippets that exhibit distinctive patterns.
In cybersecurity, anomaly detection algorithms leverage frequency-based models to flag unusual activity. For example, a sudden spike in certain character sequences in network traffic can signal an attempt to bypass encryption or exploit a vulnerability.
Yet, hackers and spies have developed countermeasures — using randomization, obfuscation techniques, and polyalphabetic ciphers — making pure frequency analysis less effective. But in the shadowy world of espionage, where simple substitution ciphers still sometimes surface, mastery of frequency analysis remains a potent skill.




Frequency Analysis and the Art of Codebreaking Today
The story of frequency analysis is a testament to how a simple mathematical insight can wield incredible power. It’s the reason why, in many classic films, codebreakers pore over ciphertext, muttering about letter counts and patterns. Behind the scenes, this technique is often the first strike against seemingly impenetrable encryption.
What about the future? As quantum computing edges closer to reality, some experts believe traditional frequency analysis might be rendered obsolete. But even then, the core idea — that language has innate patterns — will persist in some form, perhaps as the basis for new forms of cryptographic attack or defense.
Next time you see a scrambled message, remember: somewhere deep inside, the secrets of the alphabet are quietly revealing themselves — if you know where to look.



Comments