Elliptic Curve Cryptography
elliptic curve cryptography is one of those subjects that seems simple on the surface but opens up into an endless labyrinth once you start digging.
At a Glance
- Subject: Elliptic Curve Cryptography
- Category: Cryptography, Mathematics, Computer Science
Elliptic Curve Cryptography (ECC) is a powerful approach to public-key cryptography that has gained significant traction in recent decades. Unlike the more well-known RSA algorithm, which relies on the difficulty of factoring large integers, ECC harnesses the complexity of solving discrete logarithm problems on elliptic curves over finite fields.
The Mathematical Foundations of ECC
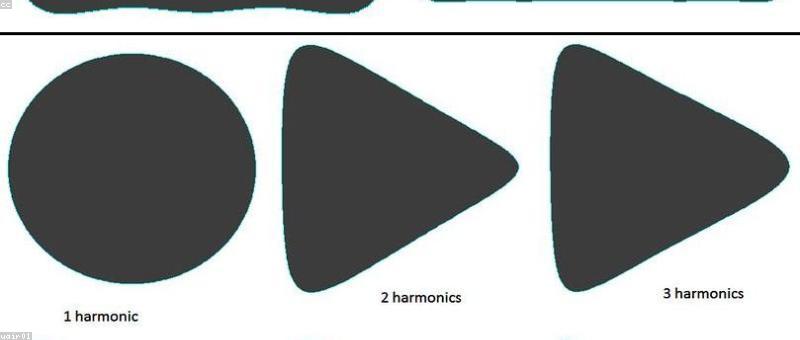
At the heart of ECC lies the theory of elliptic curves, a branch of algebraic geometry that has long fascinated mathematicians. Elliptic curves are defined by a simple equation in two variables, yet they exhibit a rich geometric structure with profound number-theoretic properties. It is this underlying mathematical complexity that makes elliptic curves well-suited for cryptographic applications.
The key to ECC is the elliptic curve discrete logarithm problem (ECDLP). Given an elliptic curve and two points on that curve, the ECDLP asks: "What is the integer k such that Q = k * P?" Finding this integer k is believed to be computationally infeasible for large, carefully chosen elliptic curves, making ECC a secure alternative to RSA.
One of the most famous applications of ECC is the Diffie-Hellman key exchange protocol. By leveraging the ECDLP, two parties can securely agree on a shared secret key over an insecure communication channel, forming the basis for encrypted communication.

The Advantages of Elliptic Curve Cryptography
Compared to RSA, ECC offers several key advantages:
- Smaller Key Sizes: For the same level of security, ECC requires much shorter key lengths than RSA. This results in faster computations, reduced storage requirements, and more efficient use of bandwidth.
- Performance: ECC algorithms are generally faster and more efficient than their RSA counterparts, making them well-suited for resource-constrained environments like mobile devices and embedded systems.
- Quantum Resistance: ECC is believed to be more resilient against attacks by quantum computers than RSA, which is a major concern for the future of cryptography.

The Standardization and Adoption of ECC
ECC has been standardized by various organizations, including the National Institute of Standards and Technology (NIST) and the Internet Engineering Task Force (IETF). These standards define specific elliptic curves and parameters that are considered secure and interoperable.
The widespread adoption of ECC has been driven by its advantages and the growing demand for secure, efficient cryptographic solutions. Major technology companies, such as Apple, Google, and Microsoft, have incorporated ECC into their products and services, further solidifying its position as a crucial component of modern cryptography.
"Elliptic curve cryptography is the future of public-key cryptography. It offers superior performance and security compared to traditional RSA, and is essential for securing the ever-growing landscape of connected devices and IoT applications." - Dr. Whitfield Diffie, cryptographer and co-inventor of the Diffie-Hellman key exchange



The Ongoing Evolution of Elliptic Curve Cryptography
As cryptography continues to evolve, researchers and practitioners are constantly exploring new frontiers in ECC. From the development of advanced algorithms and optimization techniques to the exploration of post-quantum cryptography, the field of elliptic curve cryptography remains an active area of research and innovation.
Some of the latest advancements in ECC include the exploration of pairing-based cryptography, the use of hyperelliptic curves, and the development of hardware-accelerated ECC implementations.
As the demand for secure and efficient cryptographic solutions continues to grow, the role of elliptic curve cryptography is poised to become even more crucial in the years to come. By leveraging the mathematical elegance and computational advantages of elliptic curves, ECC remains at the forefront of modern cryptographic research and practice.
Comments