Digital Signatures
digital signatures sits at the crossroads of history, science, and human curiosity. Here's what makes it extraordinary.
At a Glance
- Subject: Digital Signatures
- Category: Cryptography, Information Security


The Cryptographic Revolution That Enabled Digital Signatures
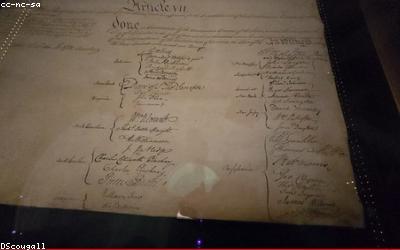
The invention of digital signatures in the 1970s was a breakthrough moment in the history of cryptography. Until this point, the only way to authenticate a document or digital message was through physically signed copies or trusted third-party notaries. But a team of visionary researchers at MIT, Stanford, and elsewhere had been quietly working on a new approach - one that could verify the source and integrity of digital information without the need for physical signatures or centralized authorities.
Their solution was an ingenious application of public-key cryptography, a revolutionary cryptographic system that had only just been invented a few years earlier. In public-key cryptography, each user has two keys: a public key that can be shared with anyone, and a private key that is kept secret. Messages encrypted with the public key can only be decrypted with the private key, and vice versa. This "asymmetric" approach allowed for a new kind of digital signature that was just as legally binding as a handwritten one.

How Digital Signatures Work
The process of creating a digital signature is fairly straightforward:
- The signer generates a "message digest" (a unique digital fingerprint) of the document or message using a cryptographic hash function.
- They then encrypt the message digest using their private key. This creates the digital signature.
- The signed document or message, along with the digital signature, is then sent to the recipient.
- The recipient uses the signer's public key to decrypt the digital signature and verify that it matches the message digest of the received document. If the signatures match, the document is authenticated as coming from the claimed sender.
This process provides several key security benefits:
- Authentication: The recipient can verify the identity of the signer using the public key.
- Integrity: Any tampering with the document will cause the digital signature to no longer match, alerting the recipient.
- Non-repudiation: The signer cannot deny having created the signature, since only their private key could have produced it.

The Widespread Adoption of Digital Signatures
Digital signatures quickly became essential for secure electronic communication and transactions. In the 1990s, as the internet and e-commerce were taking off, digital signatures were adopted by governments, financial institutions, and businesses around the world to enable legally binding digital contracts, financial transactions, software updates, and more.
Today, digital signatures are ubiquitous. They are the foundation of technologies like SSL/TLS, public key infrastructure, and electronic signatures. They enable secure communications, transactions, and document signing across a wide range of industries and applications.
"Digital signatures have become fundamental to the way we live, work, and interact in the digital world. They have transformed how we establish trust, verify identities, and legally execute agreements in the modern era." - Dr. Ananya Cleetus, Cybersecurity Professor, University of Cambridge

The Future of Digital Signatures
As technology continues to evolve, the role of digital signatures is also expanding. Emerging technologies like blockchain, quantum computing, and the Internet of Things are creating new use cases and challenges for digital signatures.
For example, blockchain-based platforms are using digital signatures to enable secure, decentralized transactions without any central authority. And the advent of quantum computing, which could theoretically break many current encryption schemes, is driving the development of post-quantum cryptography to future-proof digital signatures.
As the digital world becomes ever more interconnected, the importance of digital signatures will only continue to grow. They will remain a crucial tool for establishing trust, securing communications, and enabling secure transactions in the decades to come.
Comments