Cryptography In The Cold War
Why does cryptography in the cold war keep showing up in the most unexpected places? A deep investigation.
At a Glance
- Subject: Cryptography In The Cold War
- Category: Cold War History
- Time Period: 1947–1991
- Key Figures: William Friedman, Boris Hagelin, Claire Christensen
- Major Events: The VENONA project, SIGINT breakthroughs, the cracking of the Enigma code
The Shadow War of Codes and Ciphers
Few chapters of Cold War history are as clandestine and shrouded in mystery as the secret war of cryptography. While tanks rolled through Berlin and missiles threatened global annihilation, another battle raged quietly in the background — an invisible war fought with algorithms, ciphers, and intelligence codes. It’s a story of spies, mathematicians, and computer scientists whose work laid the groundwork for modern cybersecurity, yet remains largely unknown to the public.
One of the earliest breakthroughs came from William Friedman, a cryptographic genius who, during World War II, laid the foundation for American code-breaking efforts. His work on the development of the SIGABA machine — a cipher device used by the US government — remained unbroken by enemies until the Cold War, when adversaries relentlessly attempted to crack American secrets.


The VENONA Project: Peering into the Soviet Mind
Launching in 1943, the VENONA project was an extraordinary intelligence operation that decrypted Soviet communications. By intercepting thousands of coded messages, Western analysts uncovered the identities of Soviet spies embedded deep within American institutions. The revelation that individuals like Alger Hiss and Theodore Kaplan were Soviet agents shook the US government to its core.
"VENONA demonstrated that even the most sophisticated cryptography could be broken, provided enough resources and relentless determination."
Decoding the messages required breakthroughs in mathematical algorithms, an evolution driven by Cold War urgency. The project remained secret until 1995, long after many of its agents had been exposed. The cryptographic techniques employed were so advanced that, at the time, few believed it possible to decipher Soviet ciphers without access to their keys — yet the US proved otherwise.




Russian Innovations and the Soviet Code Machine Boom
Soviet cryptographers, inspired by the successes and failures of their Western counterparts, developed their own cipher machines. The most famous was the Crypto-1, a rotor-based device similar to the German Enigma, but with modifications that initially baffled Western cryptanalysts. Soviet cryptographic engineers like Boris Hagelin supplied much of this technology, often under suspicious circumstances involving espionage networks in Switzerland and Sweden.
The Cracking of the Enigma and Its Cold War Aftermath
The Allied victory over the Germans in World War II — partly achieved through the cracking of the German Enigma — was a turning point that influenced Cold War cryptography. The British Bletchley Park team’s success proved that even the most complex machine ciphers could be broken with ingenuity and resourcefulness. This inspired both sides during the Cold War to push encryption technology to its limits.
By the early 1950s, the US had developed the Signals Intelligence (SIGINT) capabilities that would shape Cold War espionage. The Soviets, desperate to counter these efforts, doubled down on their own encryption devices, leading to an ongoing technological arms race that continues to this day.
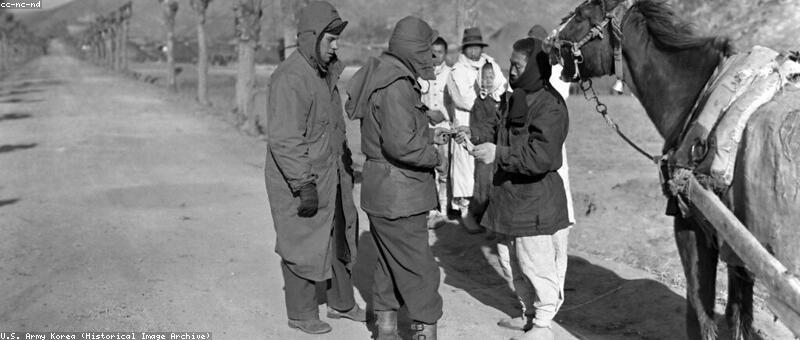
The Human Element: Spies and the Cryptographic Chase
Behind every cipher and code was a human story — spies who risked everything for a chance at decoding the enemy’s secrets. The famous Kim Philby infiltration of MI6, combined with the work of double agents and mole networks, underscored the importance of cryptography as a tool for espionage and counterespionage.
Cryptanalysts like Claire Christensen, who worked at the NSA during the late Cold War, became legends in their own right. Christensen’s work on cracking Soviet satellite communications in the 1980s helped turn the tide of espionage, revealing plans that could have destabilized entire regions.

The Cold War’s Cryptographic Legacy in Modern Cybersecurity
When the Cold War ended, the cryptographic battleground transformed from spy vs. spy into the digital age. Many techniques pioneered during that era — public key cryptography, complex algorithms, and secure communication protocols — became the backbone of modern internet security. The Cold War was, in essence, a crucible for cryptographic innovation.
Today, companies like RSA Security and AES encryption trace their roots directly to Cold War ingenuity. The clandestine, high-stakes world of espionage laid the groundwork for the encrypted chats, secure banking, and privacy tools we rely on every day.
"Without the Cold War's secret push, our digital privacy might still be a distant dream."
Comments