Cryptography Algorithms
An exhaustive look at cryptography algorithms — the facts, the myths, the rabbit holes, and the things nobody talks about.
At a Glance
- Subject: Cryptography Algorithms
- Category: Computer Security & Encryption
- First Developed: 1970s to Present
- Primary Uses: Data confidentiality, digital signatures, authentication
- Current Standards: AES, RSA, ECC, SHA-3

The Birth of Modern Cryptography: From Classics to Complexity
Cryptography didn’t start with computers. Before the digital age, armies and spies relied on simple substitution ciphers and complex letter transpositions. Julius Caesar’s shift cipher, used over two millennia ago, is the earliest example still remembered today. But the real revolution kicked off in the 1970s, when Whitfield Diffie and Martin Hellman introduced the concept of public-key cryptography in 1976, forever transforming the field.
Suddenly, encryption was no longer a secret shared in whispered circles — it could be performed openly, with keys that never needed to be exchanged secretly. This breakthrough led to the development of algorithms like RSA, named after Rivest, Shamir, and Adleman, which remains foundational to secure communications. Yet, what often surprises newcomers is how these algorithms are rooted in seemingly esoteric mathematics — prime numbers, elliptic curves, and hash functions — that seem almost magical in their power.


The Underbelly of Symmetric Encryption: AES and Its Rivals
The Advanced Encryption Standard (AES) is the bedrock of modern symmetric encryption. Chosen in 2001 after a rigorous competition, AES replaced DES (Data Encryption Standard) which had become vulnerable after decades of use. AES operates with block sizes of 128 bits and key lengths of 128, 192, or 256 bits, making it practically unbreakable with current computing power.
While AES reigns supreme for data encryption at rest and in transit, it is often paired with other algorithms to create layered security. Algorithms like RC4 or Blowfish once enjoyed popularity but now are considered obsolete due to vulnerabilities. AES remains the gold standard, but researchers are already exploring the next-generation replacements like Algorithm X, promising even greater efficiency and resistance to quantum attacks.
Asymmetric Algorithms: The Power of Public and Private Keys
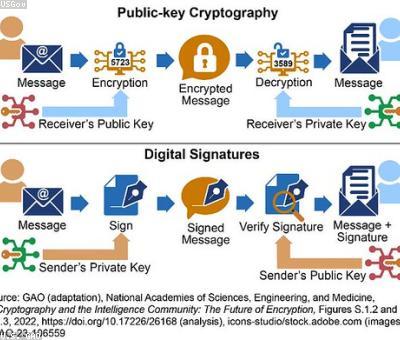
Public-key cryptography relies on a pair of keys: one public, one private. RSA remains the most well-known example. Its security is based on the difficulty of factoring large composite numbers — an elegant dance of number theory that confounds even the most powerful classical computers.
Elliptic Curve Cryptography (ECC) is a newer approach that offers comparable security with much smaller keys, making it ideal for mobile devices and IoT gadgets. In fact, the NSA approved ECC algorithms for classified communications as early as 2004, revealing how seriously governments take these techniques.
"What if quantum computers become powerful enough to break RSA? That's where lattice-based cryptography and other post-quantum algorithms come in."

Hash Functions: The Unsung Heroes of Data Integrity
Hash functions like SHA-256 and SHA-3 are the backbone of digital signatures, blockchain integrity, and password hashing. These algorithms take an input and produce a fixed-length string that appears random but is deterministic. Change even a single bit in the input, and the hash changes dramatically.
What many don’t realize is how hash functions are vulnerable to collision attacks — finding two different inputs that produce the same hash. SHA-1 was broken in 2017, leading to its deprecation. Today, SHA-3 stands as the latest standard, designed to be resistant to the most advanced attacks.




The Hidden World of Quantum-Resistant Algorithms
For decades, cryptography was built on classical mathematics — prime factorization and discrete logarithms. But quantum computers threaten to demolish these foundations overnight. Shor’s algorithm, demonstrated in 1994, shows how a sufficiently powerful quantum machine could factor large numbers exponentially faster than classical algorithms, breaking RSA and ECC.
Enter post-quantum algorithms: lattice-based, code-based, multivariate, and hash-based cryptography. NIST (National Institute of Standards and Technology) has been leading the charge, with a shortlist of candidate algorithms expected to become standards by 2024. These cryptographic beasts are designed to withstand the quantum onslaught, but the race is far from over.
"Some believe we’re only a decade away from practical quantum computers capable of breaking current encryption — so the clock is ticking."



Encryption in Practice: From Banking to Blockchain
Cryptography algorithms power everything from online banking to national security. Yet, few realize how much of their daily life depends on the meticulous, often invisible, work of these algorithms. For instance, SSL/TLS protocols use a combination of RSA, AES, and hash functions to establish secure connections between your browser and websites.
In the world of blockchain, algorithms like ECDSA (Elliptic Curve Digital Signature Algorithm) verify transactions with impressive speed and security. But a little-known fact: certain implementations have been found vulnerable to side-channel attacks, leading to a surge in hardware-based secure enclaves.
As cybersecurity threats evolve, so do cryptographic algorithms. Companies like CryptoSecure Inc. are pioneering quantum-resistant solutions for financial institutions, trying to future-proof the infrastructure against the coming storm.
It’s a wild ride — cryptography is constantly adapting, and the algorithms we trust today may be obsolete tomorrow. Yet, their core principles — mathematics, complexity, and the art of hiding secrets — remain timeless.


Comments