Cryptographic Attacks
A comprehensive deep-dive into the facts, history, and hidden connections behind cryptographic attacks — and why it matters more than you think.
At a Glance
- Subject: Cryptographic Attacks
- Category: Computer Security, Cryptography
When Codebreakers Attack: A Brief History of Cryptographic Exploits
Cryptographic attacks have been waging a covert war against the foundations of secure communication for over a century. From the trench-based codebreakers of World War I to the quantum-powered supercomputers of today, the battle for digital privacy has never been more intense.
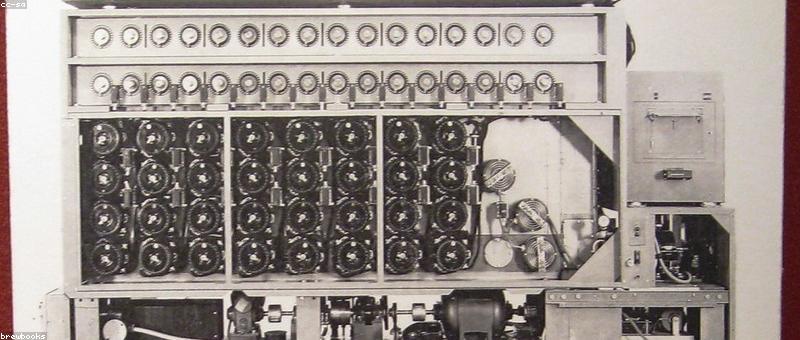
In 1917, the German military's vaunted Enigma machine was considered unbreakable — until British mathematicians at Bletchley Park devised ingenious electromechanical computers to crack its complex ciphers. This landmark achievement paved the way for the Allies' victory in the war, and set the stage for a new era of cryptographic warfare.
The Rise of Quantum Cryptanalysis
As computing power grew exponentially in the following decades, so too did the sophistication of cryptographic attacks. The development of quantum computing in the 21st century posed an especially dire threat, with powerful new algorithms capable of decimating even the most robust encryption schemes.
In 2001, mathematician Peter Shor unveiled a quantum algorithm that could efficiently factor large numbers — a capability that would render RSA encryption, the backbone of internet security, utterly useless. This alarming discovery sparked a new arms race in the world of cryptography, with researchers scrambling to develop "quantum-resistant" ciphers.
"The arrival of large-scale quantum computers would represent a technological earthquake, shattering the core of our digital security infrastructure almost overnight." — Dr. Michelle Chen, cryptography expert



The Spectre of Quantum Supremacy
While practical quantum computers remain elusive, major tech giants and government agencies are pouring billions into this high-stakes field. The prospect of quantum supremacy — the point at which quantum computers decisively outperform classical machines — looms large over the future of secure communications.
In 2019, Google made a watershed announcement: its Sycamore processor had achieved "quantum supremacy", solving a complex problem in 200 seconds that would take the world's fastest supercomputer 10,000 years. This milestone, while limited in scope, sent shockwaves through the cryptography community.
The Race to Quantum-Proof Our Digital World
Faced with the quantum apocalypse, cryptographers have been racing to develop new encryption standards that can withstand the onslaught of quantum attacks. The National Institute of Standards and Technology (NIST) is leading a global competition to identify the next generation of "quantum-resistant" cryptographic algorithms.
Candidates range from lattice-based ciphers that exploit the complexity of finding the closest vector in a lattice, to hash-based schemes that rely on the irreversibility of cryptographic hash functions. The stakes couldn't be higher, as the fate of our digital security hangs in the balance.

Preparing for the Quantum Storm
As the race to quantum-proof our digital infrastructure accelerates, experts warn that the threat of cryptographic attacks will only grow more severe. Nation-states, criminal syndicates, and rogue actors are all pouring resources into developing quantum computing capabilities that could lay waste to our current encryption standards.
The solution, it seems, lies in a multi-pronged approach: investing in quantum-resistant cryptography, fortifying our existing systems, and fundamentally rethinking the way we store and transmit sensitive data. Only by staying one step ahead of the codebreakers can we hope to safeguard our digital future.
Comments