Caesar Cipher
The complete guide to caesar cipher, written for people who want to actually understand it, not just skim the surface.
At a Glance
- Subject: Caesar Cipher
- Category: Cryptography, Information Security


The Surprising Origins of the Caesar Cipher
The Caesar cipher is one of the earliest and most well-known encryption techniques in history, yet its origins are often misunderstood. Contrary to popular belief, it was not actually invented by Julius Caesar himself, but rather named after him due to its historical association with the ancient Roman ruler.
In fact, the basic substitution cipher concept had been used for centuries before Caesar's time, with early examples dating back to ancient Sparta and Egypt. What made Caesar's version unique was the way he applied it to military communications, using a simple shift in the alphabet to encode sensitive messages during his military campaigns.
How the Caesar Cipher Works
The Caesar cipher is a type of substitution cipher, where each letter in the original message (the "plaintext") is replaced by a letter a fixed number of positions down the alphabet. This fixed number is known as the "shift" or "key" value.
For example, if the shift value is 3, then the letter 'A' would be replaced by 'D', 'B' by 'E', and so on. The last three letters of the alphabet (X, Y, Z) would wrap around and become A, B, C respectively. To decrypt the message, the process is simply reversed, with each ciphertext letter shifted back the same number of positions.
"A good cipher should be one-to-one, meaning that each plaintext letter is replaced by a unique ciphertext letter, and vice versa. The Caesar cipher meets this basic requirement."


The Caesar Cipher's Military Dominance
While the Caesar cipher may seem overly simplistic by modern standards, it proved to be an invaluable tool for secure communication during the Roman Empire's military campaigns. Caesar himself used the cipher extensively to send coded orders and intelligence reports to his generals, confident that the messages would remain unreadable to enemy forces.
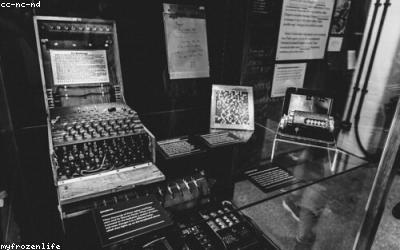
The cipher's ease of use and implementation made it a go-to choice for militaries throughout history, from the Spartans in ancient Greece to the armies of medieval Europe. Even in the 20th century, the Caesar cipher continued to see use, with the German military employing a version of it during World War I and II.
The Limits of the Caesar Cipher
Despite its historical significance and military applications, the Caesar cipher has significant limitations that made it vulnerable to cryptanalysis, even in its own time. The fixed shift value means that the ciphertext can be cracked through a simple brute-force attack, trying all 26 possible shift values until the plaintext is revealed.
Additionally, the Caesar cipher does not obscure the frequency distribution of letters in the original message, making it susceptible to frequency analysis attacks. Experienced cryptanalysts could often deduce the plaintext simply by identifying common letter patterns in the ciphertext.



The Caesar Cipher's Legacy
While the Caesar cipher may seem simplistic by today's standards, its historical significance and widespread use throughout the ages cannot be overstated. It paved the way for the development of more sophisticated symmetric-key cryptography algorithms, laying the foundation for the modern field of cryptography.
Even today, the Caesar cipher remains a valuable teaching tool, helping students and aspiring cryptographers understand the core principles of substitution ciphers and the importance of advancing encryption techniques to stay ahead of ever-evolving threats. Its enduring legacy is a testament to the ingenuity and persistence of those who have sought to conceal their communications from prying eyes.
Comments